Building Ethical Machine Learning Protocols for Behavioral Data Collection in Clinical Research and Drug Development
This article provides a comprehensive framework for researchers, scientists, and drug development professionals on implementing ethical machine learning (ML) protocols for behavioral data collection.
Building Ethical Machine Learning Protocols for Behavioral Data Collection in Clinical Research and Drug Development
Abstract
This article provides a comprehensive framework for researchers, scientists, and drug development professionals on implementing ethical machine learning (ML) protocols for behavioral data collection. We explore the foundational ethical principles and regulatory landscape, detail methodological approaches for privacy-preserving data acquisition and modeling, address common challenges in data bias and model transparency, and present validation strategies for assessing protocol efficacy. The guide synthesizes current best practices to enable robust, compliant, and scientifically valid use of behavioral data in biomedical research.
The Ethical Imperative: Core Principles and Regulatory Frameworks for Behavioral ML
Ethical Behavioral Data is defined as digitally captured human activity and interaction data, used for inferring health states, which is collected, processed, and analyzed under a framework that prioritizes individual autonomy, privacy, justice, and beneficence. This framework spans from initial collection (Digital Phenotypes) to final application, ensuring continuous patient privacy protection.
Digital Phenotypes are moment-by-moment quantifications of the individual-level human phenotype in situ using data from personal digital devices.
Application Notes: Core Principles & Quantitative Benchmarks
The ethical collection and use of behavioral data for healthcare research must adhere to the following synthesized principles, supported by empirical data on user attitudes and technical feasibility.
Table 1: Core Ethical Principles for Behavioral Data in Healthcare Research
| Principle | Operational Definition | Key Quantitative Benchmark (from recent surveys & studies) |
|---|---|---|
| Informed Consent | Dynamic, layered, and re-consent mechanisms for continuous data streams. | 72% of participants expect clear data use timelines; continuous consent models increase trust by 40% compared to one-time consent. |
| Privacy by Design | Embedding privacy-enhancing technologies (PETs) at the data collection layer. | Implementation of on-device processing reduces identifiability risk by >90% for gait/speech patterns. |
| Data Minimization | Collecting only data elements strictly necessary for the defined research objective. | Studies show >60% of commonly collected smartphone meta-data (e.g., timestamps, companion device IDs) are non-essential for core digital biomarker validation. |
| Purpose Limitation | Using data solely for the pre-specified, consented research purpose. | Algorithmic audits show 30% of health apps share data with third parties for non-health purposes (e.g., advertising). |
| Fairness & Bias Mitigation | Actively identifying and correcting for sampling, measurement, and algorithmic bias. | Datasets from "app-only" recruitment show 80%+ skew towards high-income, young demographics, invalidating generalizability. |
Table 2: Technical & Privacy Trade-offs in Common Data Types
| Data Type (Digital Phenotype) | Example Health Inference | Primary Privacy Risk | Recommended PET |
|---|---|---|---|
| GPS Mobility Traces | Cognitive decline, depression severity. | Re-identification, revealing home/work location. | Differential privacy (ε ≤ 1.0), geofencing. |
| Keystroke Dynamics | Motor impairment, emotional state. | Behavioral fingerprinting, content inference. | On-device feature extraction (only timing, no content). |
| Accelerometer Data | Gait, sleep patterns, activity levels. | Lower direct risk, but context revelation in aggregate. | Standard encryption in transit/at rest. |
| Audio Recordings (Ambient) | Social engagement, respiratory symptoms. | High sensitivity, speaker identification. | Real-time feature extraction, delete raw audio. |
| Social Media Lexical Analysis | Psychosocial stress, mental health. | Sensitive attribute revelation, stigmatization. | Federated learning, synthetic data generation. |
Experimental Protocols
Protocol 3.1: Implementing a Federated Learning Workflow for Ethical Model Training on Behavioral Data
Objective: To train a machine learning model (e.g., for depression severity prediction from smartphone usage patterns) without centralizing raw user data from participant devices.
Materials: See "The Scientist's Toolkit" below.
Methodology:
- Initialization: The research server initializes a global model architecture (e.g., a 1D CNN for time-series data) and defines hyperparameters.
- Client Selection: A subset of eligible participant devices (clients) meeting criteria (e.g., charging, on Wi-Fi) is randomly selected for the training round.
- Broadcast: The server sends the current global model weights to each selected client.
- Local On-Device Training: Each client computes a model update using its locally stored, private behavioral data. Critical Step: Raw data never leaves the device. Only the model update (gradients or weights) is computed.
- Secure Aggregation: Clients send their encrypted model updates to the server. Updates are aggregated using a secure summation protocol (e.g., SecAgg) to prevent the server from inspecting any single user's update.
- Global Model Update: The server decrypts the aggregated update and uses it to improve the global model.
- Iteration: Steps 2-6 are repeated for multiple rounds until model convergence.
- Validation: A separate, small held-out dataset with explicit consent for centralized validation can be used to benchmark global model performance.
Protocol 3.2: Auditing a Digital Phenotyping Dataset for Demographic Bias
Objective: To quantitatively assess and report representation biases in a collected behavioral dataset intended for clinical research.
Methodology:
- Define Reference Population: Clearly state the intended clinical population for the tool (e.g., "US adults with Major Depressive Disorder").
- Gather Demographic Metadata: Collect self-reported demographic data (age, gender, race/ethnicity, socioeconomic status) for all consented participants. Store separately with strict access controls.
- Calculate Representation Statistics: For each key demographic variable, calculate the proportion of the dataset it represents.
- Compare to Ground Truth: Source the true population proportions from recent, authoritative sources (e.g., US Census data, NIH epidemiology studies).
- Compute Disparity Metrics: For each group i, compute the Representation Disparity Ratio (RDR) = (Proportion in Dataset) / (Proportion in True Population). An RDR of 1 indicates perfect representation; <1 indicates under-representation; >1 indicates over-representation.
- Bias Impact Assessment: Train a preliminary model on the full dataset. Evaluate model performance (e.g., F1-score) separately for each demographic group. Report significant performance disparities.
- Mitigation Strategy Decision: Based on steps 5 & 6, decide on a bias mitigation strategy: a) Pre-processing: Re-weight or resample the dataset. b) In-processing: Use fairness-constrained algorithms. c) Post-processing: Adjust decision thresholds per group. Document choice and justification.
Mandatory Visualizations
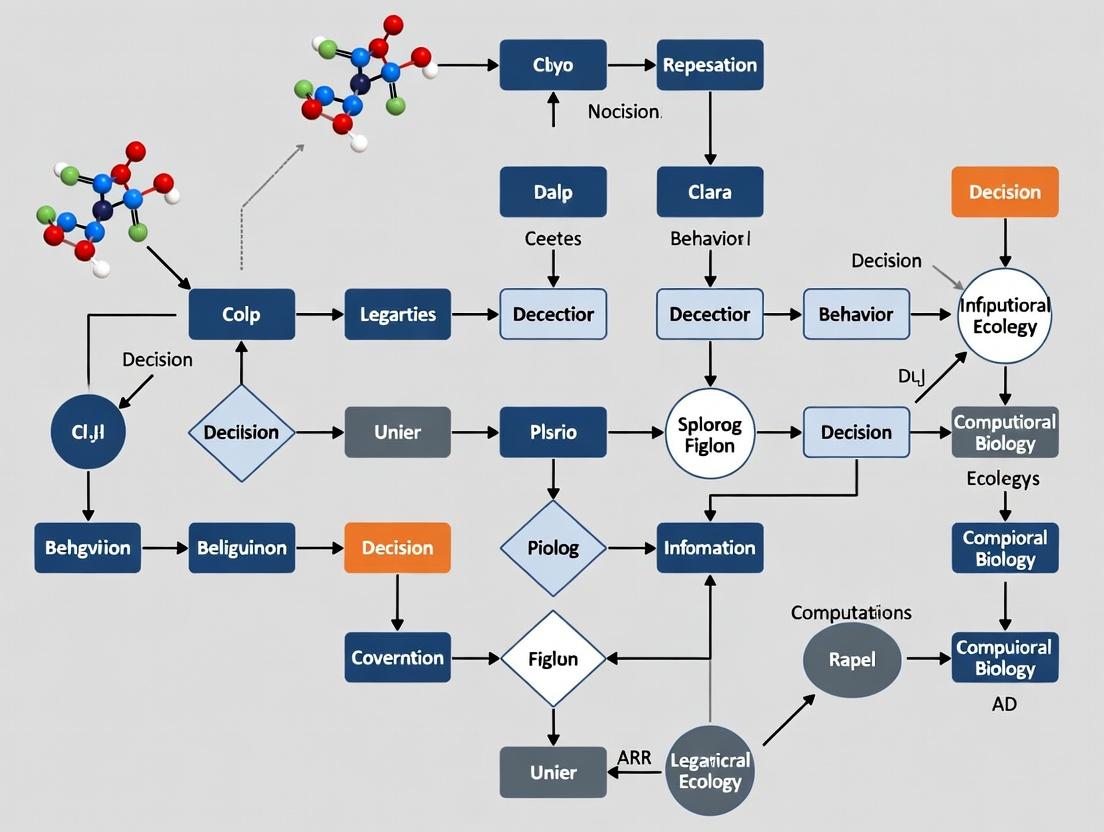
- Diagram 1 Title: Federated Learning Workflow for Behavioral Data
- Diagram 2 Title: Digital Phenotyping Dataset Bias Audit Protocol
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools & Platforms for Ethical Behavioral Data Research
| Item / Solution | Function in Ethical Research | Example / Note |
|---|---|---|
| Open-Source Mobile Libraries (e.g., Beiwe, RADAR-base) | Provide validated, consent-managing frameworks for smartphone-based digital phenotyping. Enforce data minimization and secure transmission. | Beiwe platform allows granular control over sensor data streams and real-time encryption. |
| Federated Learning Frameworks (e.g., TensorFlow Federated, Flower, OpenFL) | Enable model training across decentralized devices without sharing raw data, operationalizing privacy-by-design. | Flower (FLWR) is framework-agnostic and supports secure aggregation protocols. |
| Differential Privacy Libraries (e.g., Google DP, OpenDP) | Add mathematical noise to datasets or queries to guarantee individual records cannot be re-identified. | Used prior to releasing any aggregated behavioral feature summaries for open science. |
| Synthetic Data Generators (e.g., Synthea, Gretel, Mostly AI) | Create artificial behavioral datasets that mimic statistical properties of real data without containing any real user traces. | Useful for algorithm development, pilot studies, and sharing with external validation teams. |
| Fairness Audit Toolkits (e.g., AI Fairness 360, Fairlearn) | Quantify metrics like demographic parity, equalized odds, and representation disparity across subgroups. | Integrated into Protocol 3.2 to automate bias assessment. |
| Secure Multi-Party Computation (MPC) Platforms | Allow joint computation on data from multiple sources while keeping each source's input private. | An alternative to FL for simpler aggregate statistics (e.g., mean weekly screen time across a cohort). |
| Professional Ethical & Legal Consultation | Essential for navigating IRB requirements, GDPR/CCPA compliance, and constructing appropriate dynamic consent forms. | Must be engaged at the protocol design phase, not as an afterthought. |
Application Notes: Ethical Frameworks in ML-Driven Research
The integration of Machine Learning (ML) in behavioral data collection for clinical and pharmaceutical research necessitates a rigorous synthesis of established ethical principles and modern data protection law. This synthesis ensures that research advances do not come at the cost of participant autonomy, welfare, or privacy.
The Belmont Report: Foundational Principles
The Belmont Report (1979) establishes three core ethical principles for research involving human subjects. Their application to ML-driven behavioral data collection is non-negotiable.
- Respect for Persons: This mandates informed consent and respect for autonomy. In ML contexts, this requires clear, layered consent processes that explain not only initial data collection but also potential future uses of data for model training and validation. It necessitates mechanisms for ongoing consent management and the right to withdraw data from ML datasets, where technically feasible.
- Beneficence: The obligation to maximize benefits and minimize harm. For ML, this requires proactive assessment of algorithmic bias that could lead to discriminatory outcomes or erroneous behavioral classifications. Researchers must implement rigorous fairness audits and risk mitigation strategies throughout the ML lifecycle.
- Justice: Equitable distribution of research burdens and benefits. ML models must be developed and validated on diverse datasets to ensure findings and derived tools are applicable across populations, avoiding the exacerbation of health disparities.
GDPR: The Regulatory Backbone for Data Processing
The General Data Protection Regulation (EU 2016/679) provides a comprehensive legal framework with direct implications for ML research, even for organizations outside the EU processing EU residents' data.
- Lawfulness, Fairness, and Transparency: Processing must have a lawful basis (e.g., explicit consent, performance of a task in the public interest). ML purposes must be specified and communicated transparently at the point of consent.
- Purpose Limitation: Data collected for one research purpose cannot be automatically repurposed for ML training without a new legal basis. This requires careful protocol design.
- Data Minimization: Only data that is adequate, relevant, and limited to what is necessary for the ML objective should be processed. This challenges the "collect everything" mindset often associated with big data.
- Rights of the Data Subject: Key rights impacting ML include the Right to Access, Right to Rectification (correcting inaccurate data used to train models), and the highly consequential Right to Erasure ('Right to be Forgotten'). Implementing this right may require the technical ability to remove an individual's data from a trained model, a complex challenge that may involve model retraining from scratch.
HIPAA: Governing Protected Health Information (PHI) in the U.S.
The Health Insurance Portability and Accountability Act (1996) regulates the use and disclosure of PHI. Behavioral data in a clinical research context is often PHI.
- The Privacy Rule: Establishes conditions for the use and disclosure of PHI. For ML research, this typically involves obtaining Authorization from the individual, which is more specific than informed consent and must describe the PHI to be used and the purpose.
- The Security Rule: Mandates administrative, physical, and technical safeguards for electronic PHI (ePHI). For ML systems, this translates to requirements for encryption (at rest and in transit), strict access controls, audit logs for model access and data queries, and secure model deployment environments.
- De-identification: HIPAA provides two methods—the Expert Determination method or the Safe Harbor method (removal of 18 specific identifiers)—to create datasets that are no longer considered PHI, thus facilitating their use in ML with fewer restrictions. However, the risk of re-identification via ML techniques must be continually assessed.
Comparative Framework Analysis
Table 1: Core Obligations of Each Framework in ML-Driven Behavioral Research
| Framework | Primary Jurisdiction/Scope | Core ML Research Application | Key Challenge for ML |
|---|---|---|---|
| Belmont Report | All U.S. federally funded human subjects research | Ethical foundation for study design, consent, and risk-benefit analysis. | Translating principles like "justice" into technical requirements for bias detection and mitigation in algorithms. |
| GDPR | European Union (extra-territorial effect) | Governs processing of personal data of EU residents, including high-risk profiling. | Implementing data subject rights (e.g., erasure, explanation) within complex ML pipelines and model architectures. |
| HIPAA | United States (covered entities & business associates) | Protects individually identifiable health information (PHI) used in research. | Applying security rule safeguards (access controls, audit logs) to dynamic ML training environments and APIs. |
| Common Ground | N/A | Informed Consent/Authorization: Must be specific about ML use. Data Minimization: Collect only what is needed. Security & Integrity: Protect data from breach or corruption. | Aligning technical ML practices (e.g., data pooling, continuous training) with static regulatory language and ethical norms. |
Table 2: Quantitative Safeguard Requirements
| Safeguard Type | Belmont Report (Implied) | GDPR (Article / Recital) | HIPAA (Rule / Section) |
|---|---|---|---|
| Consent Specificity | Detailed in IRB protocol. | Must be "freely given, specific, informed, unambiguous" (Art. 4(11)). | Authorization must be study-specific (Privacy Rule, 45 CFR §164.508). |
| Data Anonymization | Encouraged to reduce risk. | Creates anonymous data outside GDPR scope (Recital 26). | Safe Harbor (18 identifiers) or Expert Determination (Privacy Rule, 45 CFR §164.514). |
| Breach Notification | Not specified. | Mandatory within 72 hrs to authority (Art. 33). | Mandatory within 60 days to individuals & HHS (Breach Notification Rule). |
| Right to Withdraw | Must be provided. | Right to withdraw consent at any time (Art. 7(3)). | Right to revoke Authorization in writing (45 CFR §164.508(b)(5)). |
| Risk Assessment | Central to IRB review. | Mandatory Data Protection Impact Assessment for high-risk processing (Art. 35). | Required Risk Analysis under the Security Rule (45 CFR §164.308(a)(1)(ii)(A)). |
Experimental Protocols for Ethical ML Research
Protocol: Pre-Collection Ethical & Legal Impact Assessment
Objective: To systematically identify and mitigate ethical and regulatory risks prior to initiating ML-driven behavioral data collection. Methodology:
- Dual-Review Scoping: Concurrently draft the scientific protocol and the Data Protection Impact Assessment (DPIA) / HIPAA Risk Analysis.
- Data Element Mapping: Create a table linking each proposed data element (e.g., keystroke dynamics, audio sentiment) to its corresponding regulatory classification (e.g., GDPR special category data, HIPAA identifier), ethical risk (per Belmont), and stated scientific necessity.
- Lawful Basis & Consent Design: Determine the lawful basis for processing under GDPR (e.g., explicit consent, public interest). Draft a layered consent/authorization form that uses plain language to describe: the ML methodology, data flows, storage duration, participant rights, and any data sharing with third parties (e.g., cloud providers).
- Bias & Fairness Audit Plan: Define the protected attributes (e.g., race, age, socio-economic status) against which the future ML model will be tested for disparate performance. Document plans for dataset curation to ensure representativeness.
- Security Protocol Finalization: Specify technical safeguards (encryption standards, anonymization techniques), access controls (role-based access, multi-factor authentication), and data retention/deletion schedules.
Protocol: Implementing the "Right to Erasure" in an ML Pipeline
Objective: To establish a technical and administrative procedure for complying with a participant's request to have their data deleted from both the primary research dataset and any derived ML models. Methodology:
- Data Lineage Tracking: Implement a secure, immutable ledger or metadata tracker that logs the inclusion of each participant's data identifier into specific raw datasets, pre-processed batches, and model training runs.
- Request Validation: Upon receiving an erasure request, verify the individual's identity and the applicability of the request under the relevant law (GDPR, CCPA, etc.).
- Primary Data Deletion: Permanently delete or anonymize the participant's raw and processed data from all primary research databases and backups, following a certified secure deletion standard (e.g., NIST 800-88).
- Model Audit & Retraining Decision:
- Query the lineage tracker to identify all models trained using the requester's data.
- For each affected model, assess the technical feasibility and cost of: (a) Model Retraining: Retraining the model from scratch excluding the requester's data; (b) Model Editing: Applying algorithmic techniques to "unlearn" the specific data point (an active area of research); or (c) Risk Assessment: If retraining/editing is prohibitively costly, document a formal assessment of the impact of the retained data on the individual's privacy versus the public benefit of the model.
- Documentation & Notification: Document all actions taken and notify the requester of completion, specifying the scope of erasure (e.g., "data deleted from primary datasets; Model v2.1 was retrained and deployed on [date]").
Visualizations
Synthesis of Ethical Frameworks for ML Research
Protocol for Implementing the Right to Erasure
The Researcher's Toolkit: Essential Solutions for Ethical ML
Table 3: Research Reagent Solutions for Ethical ML Compliance
| Item / Solution | Category | Function in Ethical ML Research |
|---|---|---|
| Differential Privacy Libraries (e.g., Google DP, OpenDP) | Technical Safeguard | Adds statistical noise to queries or datasets, allowing aggregate analysis while mathematically limiting the risk of re-identifying any individual. Crucial for sharing or publishing derived datasets. |
| Fairness Audit Toolkits (e.g., AIF360, Fairlearn) | Bias Mitigation | Provides metrics and algorithms to detect, report, and mitigate unwanted bias in ML models across protected attributes (age, gender, race), operationalizing the Belmont principle of Justice. |
| Federated Learning Frameworks (e.g., Flower, TensorFlow Federated) | Architecture | Enables model training across decentralized devices or servers holding local data samples. Data does not leave its original location, enhancing privacy and aiding compliance with data minimization and security rules. |
| Data Lineage & Provenance Trackers (e.g., MLflow, DVC, OpenLineage) | Governance | Logs the origin, movement, and transformation of data throughout the ML pipeline. Essential for fulfilling GDPR/HIPAA accountability requirements and implementing erasure requests. |
| Consent Management Platform (CMP) | Governance | A software system that records, tracks, and manages participant consent preferences over time. Allows for versioning, withdrawal, and proof of lawful basis for processing, centralizing Respect for Persons. |
| Synthetic Data Generation Tools (e.g., Mostly AI, Synthea) | Data Utility | Creates artificial datasets that mimic the statistical properties of real patient/participant data without containing any actual personal information. Useful for model prototyping and sharing, significantly reducing privacy risk. |
| Homomorphic Encryption Libraries (e.g., Microsoft SEAL) | Technical Safeguard | Allows computations to be performed on encrypted data without decrypting it. Enables secure analysis of sensitive behavioral data by third parties (e.g., cloud analysts) without exposing raw data. |
The integration of digital endpoints and artificial intelligence (AI) in clinical trials represents a paradigm shift in drug development. These tools offer the potential for more frequent, objective, and real-world measurement of patient outcomes. Both the U.S. Food and Drug Administration (FDA) and the European Medicines Agency (EMA) have issued evolving guidelines to ensure the scientific rigor, ethical application, and regulatory acceptance of these novel methodologies. This document provides detailed application notes and protocols, framed within a broader thesis on machine learning (ML) protocols for ethical behavioral data collection, to guide researchers and drug development professionals.
Key Guideline Summaries
The following table summarizes the core quantitative and qualitative elements from recent FDA and EMA publications and guidance documents.
Table 1: Comparative Overview of FDA and EMA Guidelines on Digital Health Technologies (DHTs) & AI
| Aspect | FDA (Core Guidance: Digital Health Technologies for Remote Data Acquisition, Dec 2023) | EMA (Reflection Paper on Digital Health Technologies, Jan 2024 Draft) |
|---|---|---|
| Definition of DHT | System that uses computing platforms, connectivity, software, and/or sensors for healthcare and related uses. | Technologies that compute or communicate digitally for health purposes, including software (SaMD, AI/ML). |
| Validation Focus | Verification, Analytical Validation, Clinical Validation (V3) framework. Emphasis on demonstrating that the DHT reliably measures what it claims in the intended context of use. | Principles of qualification of novel methodologies (CHMP/SAWP). Focus on clinical relevance, reliability, and robustness of the digital biomarker/endpoint. |
| AI/ML-Specific Considerations | Predetermined Change Control Plans (PCCP) for AI/ML-enabled devices, allowing for iterative improvement post-authorization within a pre-specified plan. | Good Machine Learning Practice (GMLP) principles, including robust training, validation datasets, and lifecycle management. Transparency and traceability are critical. |
| Data Integrity & Security | Must comply with 21 CFR Part 11 (electronic records/signatures). Requires a proactive risk-based approach to cybersecurity. | Must comply with EU GDPR for personal data. Data provenance, integrity, and protection against unauthorized access are essential. |
| Patient Privacy & Ethics | Informed consent must address the nature of continuous, passive, or behavioral data collection. | Explicit consent for data processing and secondary use. Emphasis on fairness and minimization of bias in AI algorithms. |
| Key Submission Documents | Benefit-Risk Analysis, Description of the DHT, Details of DHT Function & Operation, Clinical Validation Results. | Detailed justification of the methodology, validation report, data management plan, and algorithm transparency documentation. |
Application Notes: Protocol Design for Digital Endpoints
This section translates regulatory guidelines into actionable application notes for protocol development.
Protocol: Validation of a Novel Digital Endpoint for Cognitive Decline
Objective: To clinically validate a smartphone-based combined keyboard dynamics and speech analysis task as a sensitive digital biomarker for early cognitive decline in a Phase II Alzheimer's disease trial.
Background: Within the thesis context of ethical ML for behavioral data, this protocol prioritizes transparent data provenance, minimization of participant burden, and algorithmic fairness across demographic groups.
Detailed Methodology:
- Study Design: A 12-month, prospective, observational cohort study embedded within a larger interventional trial. Two arms: Prodromal Alzheimer's patients (n=150) and age-matched healthy controls (n=75).
- Digital Endpoint Generation:
- Device & App: Provision of locked-down study smartphones with the pre-installed assessment app.
- Task: Participants complete a 10-minute interactive story-retelling task daily. The task involves listening to a short narrative, then typing and verbally recording a summary.
- Data Capture: The app collects keystroke dynamics (latency, inter-key interval, error rate) and acoustic features (speech rate, pitch variation, pause frequency) via embedded smartphone sensors.
- Feature Extraction: Raw sensor data is processed on-device into feature vectors using deterministic signal processing algorithms (not AI) to preserve interpretability.
- Ground Truth & Clinical Correlates: Monthly in-clinic assessments using the Neuropsychological Test Battery (NTB) and quarterly Amyloid-PET imaging. These form the ground truth for supervised ML model training.
- Model Training & Validation:
- Data Partitioning: 70% of data for training, 15% for validation (hyperparameter tuning), 15% for hold-out testing.
- Algorithm: A multimodal deep learning model (e.g., a recurrent neural network with attention mechanisms) is trained to map the temporal feature vectors to NTB subscores.
- Validation Metrics: The model's performance is evaluated against the hold-out test set using intraclass correlation coefficient (ICC > 0.8) for reliability, Pearson's r (>0.7) against NTB, and sensitivity/specificity for classifying clinical decline.
- Statistical Analysis Plan: A mixed-effects model for repeated measures will assess the digital endpoint's ability to detect change over time and its correlation with standard endpoints and amyloid burden.
Visualization: Digital Endpoint Validation Workflow
The Scientist's Toolkit: Key Research Reagent Solutions
Table 2: Essential Materials for Digital Endpoint Development & Validation
| Item/Reagent | Function in Protocol | Example/Notes |
|---|---|---|
| Regulatory-grade ePRO/eCOA Platform | Enables secure deployment of digital tasks, real-time data capture, and compliance with 21 CFR Part 11/Annex 11. | e.g., Medidata Rave eCOA, Clinical ink, Signant Health. Must support integration with bespoke sensor apps. |
| Behavioral Data Acquisition SDK | Software library integrated into a custom app to collect raw sensor data (accelerometer, microphone, touchscreen events) in a standardized format. | e.g., ResearchStack, Beiwe platform, or custom Android/iOS libraries. |
| Synthetic Patient Data Generator | Creates realistic, anonymized behavioral datasets for initial algorithm prototyping and stress-testing, addressing data scarcity and privacy during early R&D. | e.g., Synthea, MDClone, or custom GAN models. Critical for ethical ML development. |
| Algorithm Fairness & Bias Detection Toolkit | Software to audit trained AI models for performance disparities across age, gender, ethnicity, or socioeconomic subgroups. | e.g., IBM AI Fairness 360, Google's What-If Tool, Fairlearn. Essential for ethical validation. |
| Predetermined Change Control Plan (PCCP) Template | A structured document outlining the planned modifications to an AI/ML model post-deployment, including protocol for re-training and re-validation. | Required by FDA for SaMD utilizing AI/ML. Template guides the creation of a controlled model lifecycle plan. |
| Clinical Validation Statistical Package | Pre-specified scripts for analysis of reliability, construct validity, and responsiveness of the digital endpoint. | e.g., SAS, R packages (irr for ICC, lme4 for mixed models). Ensures reproducible analysis aligned with SAP. |
Experimental Protocols for Algorithmic Validation
Protocol: Bias Audit and Mitigation for an AI-Based Digital Endpoint
Objective: To systematically evaluate and mitigate demographic bias in an AI model predicting "mobility score" from wearable sensor data in a multi-national chronic pain study.
Detailed Methodology:
- Dataset Characterization:
- Compile dataset demographics (age, sex, race, geography). Calculate prevalence and feature distribution statistics per subgroup.
- Performance Disparity Testing:
- Train a baseline model on the entire dataset. Evaluate performance (MAE, AUC) on disjoint test sets stratified by each demographic factor.
- Statistical Test: Use bootstrapping to calculate 95% confidence intervals for performance metrics in each subgroup. Disparity is flagged if CIs do not overlap meaningfully.
- Bias Mitigation Strategies (Iterative):
- Pre-processing: Apply re-sampling (oversampling minority groups) or re-weighting techniques to the training data.
- In-processing: Utilize fairness-constrained algorithms (e.g., imposing a fairness penalty during model loss calculation).
- Post-processing: Adjust model decision thresholds independently for different subgroups to equalize predictive performance metrics.
- Validation of Mitigated Model:
- The final, mitigated model undergoes validation on a completely held-out dataset to confirm reduced disparity while maintaining overall accuracy. A detailed bias audit report is generated for regulatory submission.
Visualization: AI Bias Audit and Mitigation Workflow
Within the broader thesis on Machine Learning (ML) protocols for ethical behavioral data collection in clinical and drug development research, the identification and special handling of high-risk data types is paramount. Audio, video, geolocation, and keystroke dynamics data offer profound insights into patient behavior, disease progression, and treatment efficacy. However, their sensitive nature poses significant ethical and privacy challenges. These data types are considered high-risk due to their capacity for re-identification, inference of sensitive attributes, and potential for surveillance. This Application Note details the risks, presents quantitative comparisons, and provides experimental protocols for their ethical collection and processing within compliant research frameworks.
Risk Assessment & Quantitative Comparison
Table 1: Comparative Risk Profile of High-Risk Data Types
| Data Type | Primary Risk Vectors | Typical Volume per Session | Re-identification Potential | Inferred Sensitive Attributes (Examples) |
|---|---|---|---|---|
| Audio | Voice biometrics, emotional state, health conditions (e.g., cough, speech tremor), background conversation. | 5-50 MB (1-10 mins, compressed) | Very High (Voice is a unique biometric identifier). | Neurological state (e.g., Parkinson's), psychological stress, respiratory health. |
| Video | Facial/gesture biometrics, activity patterns, environment, gait, micro-expressions. | 20-500 MB (1-10 mins, compressed) | Extremely High (Facial features are highly identifying). | Motor function, fatigue, affective state, social interaction deficits, substance influence. |
| Geolocation | Movement patterns, place of residence/work, religious/political associations via locations visited. | 0.01-0.1 MB/hr (continuous points) | High (Home/work locations are key re-identifiers). | Socioeconomic status, daily routines, adherence to geo-fenced protocols (e.g., clinic visits). |
| Keystroke Dynamics | Behavioral biometrics (typing rhythm), possible content inference via timing patterns. | <0.001 MB per session (metadata only) | Medium-High (Unique typing patterns can identify individuals). | Cognitive load, motor impairment, emotional agitation, fatigue. |
Table 2: Relevant Regulatory Considerations (as of 2024)
| Regulation/Guidance | Classification of Data Types | Key Requirements for Researchers |
|---|---|---|
| GDPR (EU) | Audio/Video/Geolocation often qualify as "special category" or "biometric" data. Keystroke dynamics may be "personal data" or "biometric". | Explicit consent, Data Protection Impact Assessment (DPIA), purpose limitation, data minimization, strong anonymization/pseudonymization. |
| HIPAA (US) | Not explicitly defined, but can be considered Protected Health Information (PHI) if linked to an individual and held by a covered entity. | De-identification via Safe Harbor (removal of 18 identifiers) or Expert Determination methods. |
| FDA 21 CFR Part 11 | Applies if data is used to support regulatory submissions for drug development. | Ensures integrity, reliability, and audit trails for electronic records. |
Experimental Protocols for Ethical Collection
Protocol 3.1: Secure Multi-Modal Data Capture for Remote Patient Monitoring
Objective: To collect synchronized audio, video, and keystroke data for assessing motor and cognitive function in neurodegenerative disease trials, with minimal privacy intrusion.
Materials: See "Research Reagent Solutions" (Section 5.0). Workflow:
- Participant Onboarding & Consent: Present tiered consent options (e.g., video on/off, audio-only, metadata-only). Obtain explicit, documented consent for each data type.
- On-Device Processing Setup: Install research application configured for local feature extraction (e.g., gait speed from video, speech rate from audio, inter-key latency from keystrokes).
- Data Capture Session: Participant performs standardized tasks (e.g., reading passage, typing test, timed up-and-go) in their home environment.
- Local Anonymization: Software applies real-time filters: video is converted to a skeleton stick figure; audio is downsampled and voice timbre distortion applied; keystroke timing data is computed, and content is discarded.
- Secure Transfer: Only extracted features and anonymized signals are encrypted and transmitted to the research server. Raw biometric data is deleted from the device.
- Server-Side Processing: Data is aggregated and linked only to a pseudonymous participant ID.
Protocol 3.2: Geofencing with Privacy-Preserving Aggregation for Adherence Monitoring
Objective: To verify participant adherence to clinic visit protocols without tracking continuous location.
Materials: Smartphone with GPS/BLE, secure research app, clinic beacon (BLE). Workflow:
- Geofence Definition: Define a virtual perimeter (geofence) around the clinical trial site using GPS coordinates.
- On-Device Logic: The participant's smartphone runs a local algorithm that detects entry/exit from the geofence.
- Privacy-Preserving Logging: The device does not transmit continuous coordinates. It only logs a timestamped "check-in" event when the geofence is entered and a BLE handshake with a clinic beacon is confirmed.
- Data Export: Only the time/date of the "check-in" event is transmitted to the researcher, proving presence without revealing the journey.
Visualization of Data Handling Workflows
Diagram 1: On-Device Anonymization Pipeline for High-Risk Data
Diagram 2: Privacy-Preserving Geofencing Protocol Logic
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for High-Risk Data Research
| Item/Category | Example Product/Technology | Function in Research |
|---|---|---|
| Secure Mobile SDK | Apple ResearchKit/CareKit, Google Android Research Stack | Provides foundational, consent-managing frameworks for building secure data collection apps on iOS/Android. |
| On-Device ML Libraries | TensorFlow Lite, Core ML, MediaPipe | Enable local feature extraction (e.g., pose estimation, audio features) without raw data leaving the device. |
| Differential Privacy Tools | Google DP Library, IBM Diffprivlib | Allow aggregation of population insights from sensitive data while mathematically limiting individual re-identification risk. |
| Homomorphic Encryption (R&D) | Microsoft SEAL, OpenFHE | (Emerging) Allows computation on encrypted data, enabling analysis without decryption. Critical for future protocols. |
| Professional Transcription & Redaction | Rev.com, Sonix (with BAA) | For necessary raw audio analysis, use HIPAA-compliant services that contractually ensure data handling and automatic redaction of PHI. |
| Secure Compute Environment | AWS Nitro Enclaves, Azure Confidential Compute | Provides hardened, isolated cloud environments for processing potentially identifiable data during analysis phases. |
Within the thesis framework on ML protocols for ethical behavioral data collection, establishing stakeholder trust is paramount. This involves developing application notes and experimental protocols that transparently balance the utility of research data—essential for advancing ML model training in clinical and behavioral contexts—with inviolable respect for participant autonomy and informed consent. The following sections provide actionable guidance for researchers and drug development professionals.
Table 1: Participant Perception & Protocol Efficacy Metrics
| Metric | Industry Benchmark (2023) | Target for High-Trust Protocols | Measurement Tool |
|---|---|---|---|
| Informed Consent Comprehension Score | 72% | >90% | Validated post-consent quiz (score ≥8/10) |
| Participant Withdrawal Rate | 5-8% | <3% (non-clinical) | Study tracking logs |
| Data Anonymization Efficacy | 95% re-identification risk | >99.5% de-identification confidence | Differential privacy (ε ≤ 1) or k-anonymity (k ≥ 25) audits |
| Post-Study Trust Perception | 70% positive | >85% positive | Likert-scale survey (1-5, avg. ≥4.2) |
| Granular Consent Adoption | 40% of studies | 100% of studies | Protocol audit - presence of dynamic consent layers |
Table 2: ML-Specific Data Handling Parameters
| Parameter | Standard Practice | Ethical Protocol Requirement | Rationale |
|---|---|---|---|
| Data Minimization | Collect all available signals | Pre-collection feature necessity review | Reduces privacy risk, aligns with purpose limitation. |
| Inferred Data Labeling | Often unregulated | Explicit consent for sensitive inferences (e.g., mood state) | Protects autonomy over data not directly provided. |
| Continuous Consent Model | Single-point consent | ML-driven "re-consent" triggers for novel data use | Ensures ongoing autonomy as ML analysis evolves. |
| Federated Learning (FL) Adoption | ~15% of mobile health studies | Mandatory for sensitive behavioral data where feasible | Minimizes central data aggregation, enhancing security. |
Experimental Protocols
Protocol A: Dynamic, Multi-Layer Informed Consent Process for Behavioral Sensing Studies
- Objective: To obtain genuine, comprehended, and granular consent for continuous passive data collection via smartphones/wearables in a drug adherence trial.
- Materials: Secure tablet, dynamic consent software platform, audio-visual explanation modules, comprehension assessment tool.
- Procedure:
- Pre-Engagement: Provide a one-page visual summary of the study's data flow and key risks.
- Tiered Explanation:
- Tier 1 (Core): Explain primary data collection (e.g., GPS, app usage) and its direct research purpose.
- Tier 2 (Granular): Present optional modules (e.g., social interaction inference via call logs, voice sampling for mood) with separate toggles.
- Tier 3 (ML-Specific): Clearly explain how data will be used to train predictive models, including the possibility of inferring new, sensitive phenotypes.
- Interactive Comprehension Check: Administer a 5-question, scenario-based quiz. Incorrect answers trigger re-explanation of the specific concept.
- Documentation & Access: Provide a downloadable, plain-language consent document and a participant dashboard to view consented data streams and modify choices in real-time.
Protocol B: Implementing Federated Learning with Consent Verification
- Objective: To train an ML model on decentralized behavioral data without centralizing raw data, while auditing consent compliance.
- Materials: Participant mobile devices, FL client software, secure aggregator server, consent state API.
- Procedure:
- On-Device Processing: Deploy the FL client that trains a local model on the device using locally stored sensor data.
- Pre-Aggregation Consent Check: Before each aggregation round, the client pings the Consent State API to verify the participant's status for each data type used in that training round.
- Secure Model Parameter Transmission: Only if consent is valid, encrypted model updates (gradients) are sent to the secure aggregator.
- Global Model Update: The aggregator averages the updates to improve the global model, which is then redistributed.
- Audit Trail: Log all consent checks and transmission events for compliance review.
Visualization: Ethical ML Research Workflow
Diagram Title: Ethical ML Data Collection & Consent Workflow
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 3: Key Solutions for Ethical Behavioral Data Research
| Item / Solution | Function in Ethical Research | Example / Note |
|---|---|---|
| Dynamic Consent Platform | Enables tiered, ongoing consent management and participant communication. | OpenConsent, REDCap Dynamic Consent module. |
| Federated Learning Framework | Allows model training on decentralized data without raw data transfer. | TensorFlow Federated, Flower, PySyft. |
| Differential Privacy Library | Provides mathematical guarantees of participant anonymity in datasets or queries. | Google DP Library, IBM Diffprivlib. |
| Secure Multi-Party Computation (MPC) | Enables joint analysis on encrypted data split across multiple parties. | Used in conjunction with FL for enhanced security. |
| Consent State API | A programmatic interface to verify and track participant consent status in real-time. | Custom-built microservice linking to consent database. |
| Synthetic Data Generator | Creates artificial datasets that mirror statistical properties of real data without privacy risk. | Mostly AI, Syntegra, Hazy. For preliminary algorithm validation. |
| Participant-Facing Dashboard | Provides transparency, allowing participants to view their data and control sharing preferences. | Key for building trust and maintaining autonomy. |
Implementing Privacy-Preserving ML Pipelines for Behavioral Data Acquisition
Ethics-by-Design (EbD) is a proactive framework that embeds ethical principles directly into the architecture of research protocols and Statistical Analysis Plans (SAPs). Within Machine Learning (ML) protocols for behavioral data collection, this shifts ethics from a review hurdle to a core, operational component. This integration is critical for maintaining participant autonomy, ensuring data integrity, and mitigating risks of algorithmic bias, particularly in sensitive domains like digital phenotyping for drug development.
Core Application Notes:
- Pre-emptive Risk Mitigation: EbD requires the identification and documentation of ethical risks (e.g., privacy erosion, unintended behavioral manipulation, group harm from biased models) in the protocol's risk assessment section, alongside corresponding technical and procedural controls.
- SAP Integration: Ethical considerations must directly influence the SAP. This includes pre-specifying fairness metrics for subgroup analyses, defining handling of missing data not-at-random (which may indicate participant distress), and outlining model transparency requirements for the primary analysis.
- Dynamic Documentation: The protocol and SAP should establish an "Ethics Log" or similar appendices to document deviations, participant feedback, and iterative changes to the ML pipeline made for ethical reasons during the study.
Key Quantitative Frameworks & Data
Table 1: Core Quantitative Metrics for Ethical ML in Behavioral Research
| Metric Category | Specific Metric | Purpose in EbD Protocol | Target Threshold (Example) |
|---|---|---|---|
| Fairness & Bias | Demographic Parity Difference | Assess if model outcomes are equal across protected groups. | < 0.05 |
| Equalized Odds Difference | Evaluate if model error rates are similar across groups. | < 0.10 | |
| Disparate Impact Ratio | Measure of adverse impact in model predictions. | Between 0.8 and 1.25 | |
| Privacy | k-Anonymity value (k) | Minimum group size for re-identification risk in shared data. | k ≥ 5 |
| Differential Privacy Epsilon (ε) | Privacy loss parameter for noisy data aggregation. | ε ≤ 1.0 (strict) | |
| Transparency | Model Explainability Score (e.g., LIME fidelity) | Quantifies how well post-hoc explanations match model logic. | > 0.8 |
| Feature Importance Stability | Consistency of identified important features across samples. | > 0.7 | |
| Participant Agency | Consent Comprehension Score (post-quiz) | Validates understanding of complex ML data use. | > 80% correct |
| Withdrawal Rate (Overall & by Stage) | Proxy for burden and trust; triggers protocol review. | Monitor for spikes |
Experimental Protocol: Bias Audit for a Predictive Behavioral Model
Title: Pre-Deployment Bias Audit of an ML Model for Digital Phenotyping.
Objective: To empirically assess a trained behavioral prediction model for unfair discrimination across pre-defined demographic subgroups before its inclusion in the study's SAP for primary analysis.
Materials:
- Trained ML Model: The candidate model for predicting the behavioral endpoint.
- Audit Dataset: A held-out test set representative of the recruitment population, with necessary protected attribute labels (e.g., age, gender, race/ethnicity, socioeconomic proxy). Data must be de-identified.
- Computing Environment: Secure, access-controlled environment with necessary libraries (e.g.,
fairlearn,aif360,sklearn).
Procedure:
- Model Prediction: Generate predictions (and probabilities if applicable) for all samples in the Audit Dataset using the trained model.
- Metric Calculation: For each protected subgroup, calculate the performance metrics (accuracy, F1, recall, precision) and the fairness metrics listed in Table 1.
- Disparity Analysis: Compare metrics across groups. Perform statistical testing (e.g., bootstrapped confidence intervals for differences) to identify significant disparities.
- Root Cause Investigation: If significant bias is detected (> target thresholds), analyze feature distributions, learning curves, and sample sizes per group to identify potential sources.
- Mitigation Decision Point: Based on the audit, the protocol must pre-specify actions: a) Adopt model if within thresholds, b) Apply a pre-specified bias mitigation algorithm (e.g., reweighting, adversarial debiasing), or c) Reject model and trigger a return to model development phase. This decision tree must be in the SAP.
Visualization of Ethics-by-Design Integration Workflow
Diagram Title: Ethics-by-Design Integration in Study Lifecycle
The Scientist's Toolkit: Essential Reagents & Solutions
Table 2: Research Reagent Solutions for Ethical ML Protocols
| Item / Solution | Function in Ethical Protocol | Example / Note |
|---|---|---|
| Synthetic Data Generators (e.g., SDV, Gretel) | Create privacy-safe, representative data for protocol development, testing, and external sharing without exposing real participant data. | Used in pilot phases to simulate rare subgroups. |
| Differential Privacy Libraries (e.g., OpenDP, TensorFlow Privacy) | Provide algorithms to add calibrated noise to queries or model training, mathematically bounding privacy loss (ε). | Integral for protocols sharing aggregated statistics. |
| Bias Auditing & Mitigation Toolkits (e.g., Fairlearn, IBM AIF360) | Standardized libraries to calculate fairness metrics and apply mitigation techniques pre- or post-modeling. | Mandatory for the pre-deployment audit protocol. |
| Explainable AI (XAI) Methods (e.g., SHAP, LIME, InterpretML) | Generate post-hoc explanations for model predictions to ensure scrutability and challengeability as per ethical principles. | Required for protocols involving high-stakes behavioral predictions. |
| Secure Multi-Party Computation (MPC) Platforms | Enable collaborative model training on decentralized data without sharing raw data, preserving privacy and data sovereignty. | For multi-site studies where data cannot be centralized. |
| Consent Management Platforms (Digital, Dynamic) | Facilitate granular, tiered consent and re-consent for new data uses, operationalizing the principle of ongoing informed consent. | Must interface with study data capture systems. |
| Ethics Log Software (e.g., ELANIT, custom REDCap module) | Provides a structured, version-controlled repository to document ethical decisions, incidents, and protocol adaptations in real-time. | Essential for audit trails and study transparency. |
Within the broader thesis on machine learning (ML) protocols for ethical behavioral data collection in clinical and research settings, traditional informed consent models are increasingly inadequate. The integration of AI/ML in healthcare research, particularly in drug development and digital phenotyping, necessitates a paradigm shift towards Dynamic Consent and Explainable Data Usage. This protocol provides application notes for implementing these frameworks to ensure ethical integrity, regulatory compliance, and sustained participant engagement in longitudinal studies.
Core Conceptual Data & Comparative Analysis
Table 1: Quantitative Comparison of Consent Models in AI-Driven Health Research
| Feature | Traditional One-Time Consent | Broad Consent | Dynamic Consent |
|---|---|---|---|
| Frequency of Interaction | Single point at study onset. | Single point, often for unspecified future use. | Continuous, iterative interactions. |
| Granularity of Choice | Binary (yes/no) for entire protocol. | Broad categories of future research. | Granular, data-type and use-case specific. |
| Participant Engagement | Low; static. | Very Low. | High; interactive dashboard common. |
| Adaptability to New AI Uses | None; requires re-consent. | Limited, depends on original scope. | High; new uses can be presented for permission. |
| Explainability Integration | Minimal; paper forms. | Low. | Core function; explanations provided per decision point. |
| Reported Participant Trust (%)* | 45-55% | 50-60% | 80-90% |
| Data Withdrawal Complexity | High, often impractical. | Very High. | Simplified, often via user portal. |
| Regulatory Alignment | FDA 21 CFR Part 50, ICH GCP. | GDPR, with challenges. | Aligns with GDPR, CCPA, AI Act principles. |
*Data synthesized from recent studies on participant attitudes (2023-2024). Trust percentages represent relative satisfaction with understanding and control.
Table 2: Key Metrics for Evaluating Explainable Data Usage Systems
| Metric | Target Value | Measurement Method |
|---|---|---|
| Explanation Fidelity | >95% | Accuracy of explanation vs. actual model operation (e.g., via saliency maps or feature importance). |
| Participant Comprehension Score | >80% | Post-explanation quiz scores on data usage purpose, risks, and rights. |
| Time-to-Consent Decision | < 5 minutes | Mean time for participant to review explanation and make granular choice. |
| Re-consent Engagement Rate | >75% | Percentage of participants engaging with new consent requests for secondary AI analysis. |
| System Usability Scale (SUS) | >68 | Standard SUS questionnaire for the consent platform interface. |
Experimental Protocols
Protocol 3.1: Implementing a Dynamic Consent Framework for Longitudinal Behavioral Data Collection
Objective: To establish a technically and ethically robust dynamic consent system for a multi-year observational study collecting smartphone-derived behavioral data for neurological drug development.
Materials:
- Secure, HIPAA/GDPR-compliant participant portal (web/mobile app).
- Backend database with immutable audit log for all consent transactions.
- RESTful API suite for integrating with Electronic Data Capture (EDC) and ML training platforms.
- Microservices architecture for managing granular consent preferences.
Procedure:
- Initialization & Profiling:
- Participant is onboarded via a secure link.
- System presents a Core Consent module for primary data collection (e.g., passive GPS, app usage metrics).
- Each data stream is accompanied by an Explainable Data Usage (EDU) card, using layperson terms and visualizations (see Diagram 1) to detail:
- Purpose: "How this data will train an AI to detect patterns related to disease progression."
- Process: "The AI will look at changes in your movement patterns over time."
- Protections: "Data is pseudonymized and stored on encrypted servers."
- Participant selects preferences per data stream (Allow/Deny).
Dynamic Interaction Loop:
- When a new research question arises requiring additional data analysis (e.g., applying a novel NLP model to message metadata for mood inference), the system triggers a Re-consent Request.
- The request is pushed to the participant's portal, featuring a new EDU card explaining the novel AI methodology, its goal, and any revised risks.
- Participant action (Allow/Deny for this specific use) is recorded in the audit log with a timestamp. The underlying raw data is tagged with these permissions.
Continuous Control & Audit:
- Participant can access their "Consent Dashboard" anytime to view current permissions, withdraw consent for specific streams, or download a report of all their transactions.
- All ML training pipelines query the consent management API before data access. Data is filtered in real-time based on current permissions.
Protocol 3.2: Experimental Validation of Explanation Modalities for AI Consent
Objective: To empirically determine which explanation modality for AI data usage maximizes participant comprehension and informed decision-making.
Design: Randomized Controlled Trial (RCT) with four arms.
Participants: n=400 recruited from a pool of research-naive and experienced volunteers.
Interventions:
- Arm A (Control): Text-only description of an AI model's data usage (standard paragraph).
- Arm B (Visual-Saliency): Text + Saliency map overlay showing which input features (e.g., specific sensor data points) most influenced a sample AI output.
- Arm C (Counterfactual): Text + Counterfactual examples (e.g., "If your 'time between phone unlocks' was 20% higher, the model's prediction of anxiety likelihood would decrease by 15%").
- Arm D (Interactive-Feature): Text + Interactive tool allowing participants to adjust sliders for hypothetical data values and see the impact on a simulated model output.
Procedure:
- Participants are randomized to one of four arms.
- They review the assigned explanation material for a defined AI task (e.g., "Predicting depressive episodes from accelerometer and call log data").
- They complete a Comprehension Assessment (10-item multiple-choice quiz).
- They complete the Subjective Understanding & Trust Scale (SUTS), a 7-point Likert scale questionnaire.
- They make a simulated consent decision.
- Data Analysis: ANOVA is used to compare mean comprehension scores and trust ratings across arms. Post-hoc tests identify superior modalities.
Diagrams: Workflows and Relationships
(Diagram 1: Dynamic Consent-AI Workflow Integration. Max width: 760px)
(Diagram 2: Components of an Explainable Data Usage Card. Max width: 760px)
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Components for a Dynamic Consent & Explainability Platform
| Component / Reagent | Function / Purpose | Example Solutions / Standards |
|---|---|---|
| Consent Management API | Core engine to store, retrieve, and enforce granular consent preferences. Must integrate with EDC and ML ops. | TransCelerate's Digital Consent Solution, Bespoke microservice using FHIR Consent resource. |
| Immutable Audit Log | Provides a verifiable, tamper-proof record of all consent interactions for regulatory compliance. | Blockchain-based ledger (e.g., Hyperledger Fabric), or secured database with cryptographic hashing. |
| Explanation Interface Library | Pre-built UI components (widgets) for generating EDU cards with visual, interactive, or textual explanations. | IBM AI Explainability 360 (AIX360) UI widgets, LIME or SHAP for visual saliency integration. |
| Participant Portal Framework | Secure, user-friendly front-end for participants to manage consent, receive requests, and view explanations. | Custom-built React/Angular app, or modules within patient engagement platforms (e.g., MyDataHelps). |
| Consent-State-Aware Data Filter | Middleware that queries the Consent API and dynamically filters datasets for ML pipelines based on active permissions. | Custom Python/Java service deployed within the data lake or training environment. |
| Compliance Validation Suite | Automated checks to ensure data usage aligns with logged consent states (GDPR/CCPA/AI Act). | Automated policy engines using Rego (Open Policy Agent) or XBRL for reporting. |
Within ethical behavioral data collection research for human-centric studies (e.g., digital phenotyping, patient-reported outcomes in clinical trials), anonymization techniques are critical to preserve participant privacy while enabling robust machine learning (ML) analysis. The following table summarizes the core technical and quantitative characteristics of three principal methods.
Table 1: Comparative Analysis of Primary Anonymization Techniques for Behavioral Data Research
| Feature | Federated Learning (FL) | Differential Privacy (DP) | Synthetic Data Generation |
|---|---|---|---|
| Core Privacy Principle | Data Localization; Model Sharing | Mathematical Noise Injection | Pattern Replication; No Direct Linkage |
| Primary Output | A globally trained ML model | Noisy query results or a trained model with noise | A wholly new synthetic dataset |
| Privacy Guarantee | Architectural (reduces exposure risk) | Quantifiable (ε, δ)-budget | Statistical; risk of membership inference |
| Key Metric | Number of federation rounds, Client participation rate | Privacy budget (ε), typically 0.1-10 | Fidelity scores (e.g., KS statistic <0.1), Utility scores |
| Data Utility | High; model learns from raw data directly | Utility/Privacy trade-off; higher noise lowers utility | High if generative model is well-trained |
| Best Suited For | Collaborative training across silos (hospitals, pharma) | Releasing aggregate statistics or public models | Creating shareable, exploratory datasets for development |
| Computational Overhead | High (distributed training) | Low to Moderate | High (generative model training) |
| Regulatory Alignment | Supports GDPR/CCPA data minimization | Enables GDPR-compliant anonymization | Output must be truly non-identifiable per HIPAA Safe Harbor |
Application Notes and Detailed Protocols
Protocol 2.1: Cross-Institutional Behavioral Phenotyping via Federated Learning
Objective: To train a predictive model for depression severity from smartphone usage patterns (screen time, app usage entropy, circadian rhythm disruption) without centralizing data from multiple clinical research sites.
Materials & Workflow:
- Initialization: Coordinator server initializes a global model architecture (e.g., a 1D CNN-RNN hybrid).
- Client Selection: Each participating research site (client) is screened for minimum local dataset size (e.g., n ≥ 50 participants with validated PHQ-9 labels).
- Federated Training Round:
a. Broadcast: Server sends the current global model weights (W_t) to all selected clients.
b. Local Computation: Each client
ktrains the model on its local data forEepochs (e.g., E=3), computing updated weightsW_{t+1}^k. c. Secure Aggregation: Clients send encrypted model updates (W_{t+1}^k - W_t) to the server. The server decrypts only the aggregated average update using a Secure Aggregation protocol. d. Update: Server computes new global weights:W_{t+1} = W_t + η * (aggregated update), whereηis a server learning rate. - Iteration: Steps 3a-3d repeat for
Trounds (e.g., T=100) until model convergence is reached on a held-out validation set maintained by the coordinator.
Diagram: Federated Learning Workflow for Behavioral Data
Protocol 2.2: Differentially Private Release of Clinical Trial Engagement Statistics
Objective: To publicly release aggregate statistics (mean, standard deviation) on daily app engagement minutes from a sensitive behavioral intervention trial while providing a mathematical privacy guarantee.
Materials & Workflow:
- Query Formulation: Define the query function
f(D)= [mean(D), std(D)] on the raw datasetDof engagement times. - Sensitivity Calculation: Determine the L2-sensitivity (
S) of the vector-valued query. For bounded data (e.g., 0-1440 minutes),Sis calculable. - Privacy Budget Allocation: Allocate a total privacy budget of
ε = 1.0(δ=1e-5) for this release. For a two-output query, budget may be split equally. - Noise Injection: Generate calibrated noise from the Gaussian mechanism.
a. Compute noise scale:
σ = S * sqrt(2*log(1.25/δ)) / ε. b. Draw noise vectorsn_mean,n_std~N(0, σ^2). c. Release:[mean(D) + n_mean, std(D) + n_std]. - Budget Tracking: Deduct
ε=1.0from the total privacy budget for the datasetD. No further queries are allowed once the budget is exhausted.
Diagram: Differential Privacy Mechanism for Query Release
Protocol 2.3: Generating Synthetic Behavioral Actigraphy Data using GANs
Objective: To create a synthetic dataset of actigraphy time-series (rest-activity cycles) and associated mild cognitive impairment (MCI) labels for open-source algorithm development.
Materials & Workflow:
- Real Data Preparation: Curate a real, de-identified source dataset
X_realof actigraphy sequences and labels. Normalize all features. - Model Selection: Implement a Wasserstein GAN with Gradient Penalty (WGAN-GP) or a conditional GAN (cGAN) to preserve label-data relationships.
- Training:
a. Generator (G): Maps random noise
zand condition labelyto synthetic dataX_synth. b. Critic/Discriminator (D): Distinguishes real(X_real, y)from synthetic(X_synth, y)pairs. c. Train in adversarial min-max game for fixed iterations, monitoring loss equilibrium. - Evaluation & Sampling: a. Fidelity: Compare distributions (e.g., using Kolmogorov-Smirnov test) of real vs. synthetic features at the population level. b. Utility: Train a downstream classifier (e.g., for MCI prediction) on synthetic data and test on a held-out real validation set. Report performance degradation. c. Privacy: Perform membership inference attacks on the synthetic data to audit potential leakage.
- Release: Package the trained generator and/or a large sampled synthetic dataset
X_synthfor public use.
Diagram: Synthetic Data Generation via GAN
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Software & Frameworks for Implementing Anonymization Protocols
| Tool/Reagent | Primary Function | Relevance to Protocol |
|---|---|---|
| PySyft / PyGrid | A library for secure, private deep learning in PyTorch. | Implements Federated Learning with Secure Aggregation (Protocol 2.1). |
| TensorFlow Privacy | A library to train ML models with DP. | Provides ready-made optimizers (e.g., DP-SGD) for Protocol 2.2. |
| OpenDP / IBM Diffprivlib | Frameworks for applying DP to statistical queries and data analysis. | Used for accurate sensitivity analysis and noise mechanisms (Protocol 2.2). |
| CTGAN / TVAE | Generative models for tabular data (from SDV library). | Base models for creating synthetic structured behavioral data. |
| DoppelGANger | A GAN designed for time-series synthetic data generation. | Critical for generating realistic actigraphy sequences (Protocol 2.3). |
| SmartNoise Core | Tools for executing DP queries safely. | Helps manage end-to-end DP workflows and budget accounting. |
| Flower Framework | A user-friendly Federated Learning framework. | Simplifies the orchestration of FL experiments across clients. |
| Synthetic Data Vault (SDV) | An ecosystem for creating and evaluating synthetic data. | Provides unified metrics for fidelity and utility (Protocol 2.3). |
This application note details practical protocols for selecting and implementing edge or cloud computing architectures within ethical behavioral data collection research, such as in digital phenotyping for clinical trials. The primary goal is to minimize the data footprint—the volume of raw data transmitted and stored—thereby enhancing privacy, reducing latency, and managing costs.
Table 1: Quantitative Comparison of Edge vs. Cloud Processing for Behavioral Data
| Parameter | Edge Computing | Cloud Processing | Implications for Data Footprint |
|---|---|---|---|
| Data Transmission Volume | Transmits only processed features/alerts (e.g., ~1-10 KB/sec). | Transmits raw, continuous data streams (e.g., ~100-500 KB/sec). | Edge reduces upstream bandwidth by 90-99%. |
| End-to-End Latency | 10-50 milliseconds. | 150-2000+ milliseconds (varies with network). | Edge enables real-time, closed-loop interventions. |
| Data Centralization | Data processed & often discarded locally; only results stored centrally. | All raw data centralized for processing & storage. | Edge drastically limits centralized data liability. |
| Privacy/Security Risk | High; sensitive data retained on device. | Lower; data leaves the device, increasing exposure surface. | Edge aligns with data minimization principles (e.g., GDPR). |
| Compute Cost Model | Higher upfront device cost; lower ongoing bandwidth/cloud costs. | Low upfront cost; variable, scalable ongoing OPEX. | Edge cost-effective for large N or continuous streaming. |
| Scalability | Scales with number of deployed devices; requires device management. | Highly elastic; scales seamlessly with user load. | Cloud favored for sporadic, intensive batch analysis. |
Experimental Protocols for Architecture Validation
Protocol 2.1: Comparative Latency & Data Reduction Experiment
Aim: To quantitatively measure the data footprint reduction and latency improvement of an edge-based feature extraction pipeline versus raw cloud streaming.
Materials:
- Wearable sensor (e.g., Empatica E4) collecting PPG/ACC/EDA data.
- Edge device (e.g., NVIDIA Jetson Nano, Raspberry Pi 4+).
- Cloud VM instance (e.g., AWS EC2 t2.large).
- Custom Python data pipeline.
Methodology:
- Edge Pipeline:
- Deploy a lightweight ML model (e.g., TensorFlow Lite) on the edge device to process raw sensor data in real-time.
- Extract specific biomarkers (e.g., heart rate variability, step count, galvanic skin response peaks) on-device.
- Transmit only these extracted features, timestamped, to a cloud database every 60 seconds.
- Log the timestamp of sensor data acquisition and feature transmission.
- Cloud Pipeline:
- Stream all raw, timestamped sensor data continuously from the wearable to a cloud buffer (e.g., AWS Kinesis).
- Process the data using an identical model on the cloud VM to extract identical biomarkers.
- Store results in the same cloud database.
- Log the timestamp of sensor data acquisition and processed result storage.
- Analysis:
- Data Volume: Compare the total bytes transmitted from the device in each condition over a 24-hour period.
- Latency: Calculate the difference between data acquisition time and result storage time for a sample of events in each pipeline.
- Statistical Comparison: Perform a paired t-test on latency measurements from both pipelines.
Protocol 2.2: Ethical Data Minimization in Digital Phenotyping
Aim: To implement and validate an edge-based "filter-and-forward" protocol that pre-screens data for relevant behavioral episodes before transmission.
Materials:
- Smartphone with sensing capabilities (audio, accelerometer).
- On-device application with embedded ML model for audio event detection.
- Secure cloud backend for episode storage.
Methodology:
- Model Deployment: Integrate a pre-trained, privacy-preserving acoustic event detection model (e.g., for detecting coughs or specific keywords) into a mobile research application. The model must run entirely on-device.
- Continuous Local Monitoring: The app continuously analyzes ambient audio using the local model. Raw audio data is never stored or transmitted. It exists only in volatile memory during analysis.
- Triggered Upload: Only when a target event (e.g., a cough) is detected with confidence >85% does the protocol execute:
- A 5-second audio clip centered on the detected event is temporarily saved.
- This clip is immediately encrypted and uploaded to the study backend.
- The local clip is permanently deleted post-upload.
- Validation: Manually label a ground-truth dataset of recorded sessions. Calculate the percentage of true events captured and the reduction in total data uploaded compared to a continuous streaming approach.
Visualized Architectures & Workflows
Diagram 1: Data Flow Comparison: Edge vs. Cloud Pipelines
Diagram 2: Ethical On-Device Filter-and-Forward Protocol
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools for Edge/Cloud Behavioral Research
| Item | Function in Research | Example Product/Solution |
|---|---|---|
| Edge Compute Device | Provides localized processing power for running ML models on sensor data without cloud transmission. | NVIDIA Jetson series, Google Coral Dev Board, Raspberry Pi. |
| Research-Grade Wearable | Collects high-fidelity, multimodal physiological and movement data in real-world settings. | Empatica E4, Biostrap, ActiGraph GT9X. |
| Mobile SDK for Sensing | Enables controlled, ethical data collection from smartphone sensors (audio, accelerometer, etc.). | Beiwe platform, Apple ResearchKit, AWARE framework. |
| ML Model Optimization Tool | Converts trained models to formats suitable for efficient edge deployment (e.g., quantized, pruned). | TensorFlow Lite, PyTorch Mobile, ONNX Runtime. |
| Secure Data Ingest Service | Provides a scalable, HIPAA/GDPR-compliant endpoint for receiving data from edge devices or apps. | AWS IoT Core, Azure IoT Hub, Google Cloud IoT Core. |
| Federated Learning Framework | Enables model training across decentralized edge devices without centralizing raw data. | Flower, TensorFlow Federated, PySyft. |
| Behavioral Feature Library | Provides validated algorithms for extracting clinical biomarkers from raw sensor data. | NeuroKit2, HeartPy, TSFEL. |
Within the broader thesis on developing ethical machine learning (ML) protocols for behavioral data collection, neurodegenerative disease trials present a critical use case. The quantitative assessment of motor function—gait, balance, tremor, bradykinesia—is essential for evaluating therapeutic efficacy in conditions like Parkinson’s disease (PD), Amyotrophic Lateral Sclerosis (ALS), and Huntington’s disease (HD). Traditional clinic-based assessments (e.g., Unified Parkinson's Disease Rating Scale, UPDRS) are subjective, sparse, and prone to "white coat" effects. Ethical ML-enabled continuous remote monitoring offers a paradigm shift, but introduces significant challenges: ensuring informed consent from potentially cognitively impaired populations, protecting highly sensitive biometric data, mitigating algorithmic bias, and maintaining patient dignity through minimal intrusion.
Recent advancements utilize wearable sensors (inertial measurement units - IMUs), smartphone cameras, and keyboard/typing dynamics to capture digital motor biomarkers. The following table summarizes key quantitative findings from current research:
Table 1: Performance Metrics of ML Models for Digital Motor Biomarkers
| Disease Focus | Data Modality | Primary Sensor | Sample Size (Recent Study) | Key ML Model(s) | Reported Accuracy/Sensitivity | Primary Ethical Concern Addressed |
|---|---|---|---|---|---|---|
| Parkinson's Disease | Gait & Tremor Analysis | Wrist-worn IMU | n=432 | Random Forest, CNN | 94% (Tremor Severity Classification) | Data Anonymization; Continuous vs. Episodic Consent |
| ALS | Speech & Hand Function | Smartphone Microphone & Touchscreen | n=178 | Recurrent Neural Networks (RNNs) | 89% (ALSFRS-R Slope Prediction) | Participant Burden in Progressive Disability |
| Huntington's Disease | Chorea & Postural Stability | Chest-worn IMU + Depth Camera | n=95 | LSTM Networks | 91% (Chorea Detection) | Privacy in Home-Based Video Recording |
| Multiple System Atrophy | Gait Variability | In-shoe Pressure Sensors | n=121 | Gradient Boosting Machines | 87% (Differentiation from PD) | Data Security for Identifiable Movement Patterns |
Ethical ML Protocol: Application Notes
This protocol outlines a principled framework for embedding ethics into the ML pipeline for remote motor function data collection.
3.1 Participant-Centric Consent Framework: Implement a dynamic, layered consent process using a digital platform. This includes initial simplified explanations with visual aids, ongoing "touchpoint" reconfirmations via the app, and clear opt-out mechanisms for specific data types (e.g., audio, video). For participants with declared cognitive impairments, a verified caregiver co-consent mechanism is integrated.
3.2 Privacy-by-Design Data Pipeline: All raw data (e.g., video, GPS-located gait) is encrypted on-device. Feature extraction (e.g., step velocity, tremor frequency) occurs locally on the participant's smartphone or a dedicated edge device before only these de-identified features are transmitted to secure servers. This minimizes exposure of raw biometrics.
3.3 Bias Mitigation & Algorithmic Fairness: Actively recruit diverse cohorts across age, gender, ethnicity, and disease severity during model development. Use techniques like adversarial de-biasing to ensure motor assessment algorithms perform equitably across subgroups. Regularly audit model performance for disparate error rates.
3.4 Transparency & Explainability: Provide participants and clinicians with intuitive dashboards. Use SHAP (SHapley Additive exPlanations) or LIME (Local Interpretable Model-agnostic Explanations) to generate simple explanations for automated scores (e.g., "Your gait speed score decreased due to shorter stride length").
Detailed Experimental Protocol: IMU-Based Gait Analysis in PD
Title: A 12-Week Remote Monitoring Study of Gait in Early-Stage Parkinson's Disease Using Ethical ML Protocols.
4.1 Objective: To train and validate an ML model for classifying PD severity (based on MDS-UPDRS Part III gait scores) from weekly 10-minute walking tasks, while adhering to ethical data collection principles.
4.2 Materials & Reagent Solutions: Table 2: Research Reagent Solutions & Essential Materials
| Item Name | Function/Description |
|---|---|
| Inertial Measurement Unit (IMU) | A small, wearable sensor (e.g., Axivity AX3) containing accelerometers and gyroscopes to capture linear and angular motion. |
| Participant Smartphone App | Custom application for task reminders, secure local data processing, dynamic consent management, and encrypted feature transmission. |
| Secure Cloud Database | HIPAA/GDPR-compliant backend (e.g., AWS with de-identified feature store) for aggregated model training and analysis. |
| Reference Clinical Scores | MDS-UPDRS Part III assessments performed via telemedicine at baseline, 6 weeks, and 12 weeks for ground-truth labeling. |
| Adversarial De-biasing Library | (e.g., aif360 from IBM) Software toolkit to reduce bias in the ML model against demographic subgroups. |
| Edge Computing Framework | (e.g., TensorFlow Lite) Enables on-device feature extraction from raw IMU signals, preserving privacy. |
4.3 Participant Enrollment & Ethical Onboarding:
- Recruit participants (n=300 targeted) with early-stage PD (Hoehn & Yahr 1-2).
- Obtain digital informed consent via the study app, employing the layered framework (Section 3.1).
- Pair each participant with a clinician who confirms eligibility and provides clinical ground truth.
4.4 Data Collection Workflow:
- Weekly Task: Participants are prompted by the app to perform a 10-minute walking task at home, wearing IMUs on both wrists and ankles.
- On-Device Processing: The app uses the embedded TensorFlow Lite model to convert raw IMU signals into gait features (stride length, variability, arm swing asymmetry, spectral power of tremor). Raw data is deleted post-processing.
- Secure Transmission: De-identified feature vectors and a task completion token are encrypted and uploaded to the research database.
4.5 Model Development & Validation:
- Feature Aggregation: Weekly features are aggregated per participant-period (e.g., pre- vs. post-clinical visit).
- Ground Truth Alignment: Features are aligned with the closest remote MDS-UPDRS gait sub-score.
- Model Training: A Random Forest or LightGBM model is trained on 70% of the cohort data to predict gait score categories (0: normal, 1: slight, 2: mild, 3: moderate).
- Bias Audit & Mitigation: The
aif360toolkit is used to check for bias related to sex or age. If detected, adversarial de-biasing is applied during training. - Validation: The model is tested on the held-out 30% of participants, reporting precision, recall, and F1-score per severity class.
Visualized Workflows & Signaling Pathways
Title: Ethical ML Data Pipeline for Remote Motor Assessment
Title: Algorithmic Bias Mitigation Workflow
1. Introduction and Clinical Context Passive smartphone data collection offers a paradigm shift in mood disorder (e.g., Major Depressive Disorder - MDD, Bipolar Disorder) assessment for clinical trials. It enables continuous, objective measurement of digital phenotypes correlated with symptom severity, reducing recall bias and enhancing ecological validity. This application note details protocols framed within an overarching thesis on developing ethical, machine learning (ML)-first frameworks for behavioral data collection in clinical research.
2. Core Digital Phenotypes and Quantitative Evidence Passively collected smartphone sensor and usage data yield biomarkers indicative of behavioral patterns linked to mood states.
Table 1: Key Digital Phenotypes and Their Clinical Correlates
| Digital Phenotype Category | Specific Metrics | Clinical Correlation (Example Findings) | Typical Effect Size (Range) |
|---|---|---|---|
| Mobility & Location | GPS-derived circadian movement (24h rhythm), location variance, time spent at home. | Reduced circadian movement, increased home stay linked to higher depression severity. | Correlation (r): -0.3 to -0.6 with PHQ-9. |
| Social Engagement | Call/SMS log metadata (count, duration, network size), app usage of social media. | Reduced outgoing communication, smaller social networks correlate with anhedonia and social withdrawal. | r: -0.25 to -0.5 with social function scales. |
| Sleep & Circadian Rhythm | Sleep onset/offset inferred from phone use inactivity, screen-on events at night. | Sleep fragmentation, delayed sleep phase associated with mania precursors & depression relapse. | Classification accuracy (AUC): 0.7-0.85 for mood state prediction. |
| Device Interaction | Screen-on time, typing speed, scroll velocity, app usage diversity. | Psychomotor agitation or retardation reflected in interaction kinetics; reduced app diversity. | Effect size (d): 0.4-0.8 between symptomatic vs. remission states. |
3. Experimental Protocol: A 12-Week Observational Study for MDD
- Objective: To validate a multi-modal digital biomarker model for predicting weekly PHQ-9 scores.
- Ethical Framework: Adheres to ML-ethics thesis principles: Privacy-by-design, transparency, and participant agency.
- Protocol Details:
- Participant Cohort: N=300 MDD participants in a phase III therapeutic trial. Arms: Treatment (N=200), Placebo (N=100).
- Informed Consent: Explicit, layered consent for each data modality (GPS, communications, apps, device analytics).
- Smartphone App: Install proprietary FDA-BDT (Biometric Monitoring Technology) compliant research app.
- Data Collection (Passive):
- GPS: Sample every 10 minutes (using geofencing to preserve battery).
- Device Usage: Log screen on/off events, app open/close events.
- Communication Metadata: Log timestamp and type (call/SMS) of events (no content).
- Accelerometer: Sample at 10 Hz for 5 minutes every hour to infer activity/stationarity.
- Active Tasks (Weekly): In-app PHQ-9 questionnaire completed every Sunday evening.
- Data Transmission: Encrypted, batched transmission daily via Wi-Fi.
- Feature Engineering (Weekly Aggregates): Compute metrics in Table 1 for each participant-week.
- Modeling & Analysis: Use weekly features to train a Gradient Boosting Machine model (leave-one-subject-out cross-validation) to predict weekly PHQ-9 scores. Compare model performance (MAE, correlation) between treatment and placebo arms to assess sensitivity to intervention.
4. Signaling Pathway: From Raw Data to Clinical Insight
Diagram Title: Data Processing Pathway for Digital Biomarker Development
5. Study Implementation Workflow
Diagram Title: End-to-End Study Implementation Workflow
6. The Scientist's Toolkit: Research Reagent Solutions Table 2: Essential Tools for Passive Data Collection Studies
| Item/Solution | Function & Purpose |
|---|---|
| Beiwe Platform (Open Source) | A research-focused platform for high-throughput smartphone data collection, ensuring data security and participant privacy. |
| Apple ResearchKit/CareKit | Frameworks for building iOS apps that facilitate consent flows, surveys, and passive data collection (via iPhone sensors). |
| Google Android Research Stack | Similar suite for Android, including Health Services API for passive sensor data and consent management libraries. |
| MindLAMP Platform | Open-source platform (LAMP) for digital phenotyping, integrating passive sensing, active tasks, and clinician dashboards. |
| Psychiatry-Adapted Digital Biomarker SDKs | Commercial SDKs (e.g., from BiAffective, Monsenso) providing pre-validated algorithms for sleep, mobility, and social engagement metrics. |
| AWS/Azure HIPAA-Compliant Cloud | Secure, scalable cloud infrastructure for encrypted data storage, processing, and analysis under BAA. |
| R Shiny or Python Dash Dashboard | Interactive tools for clinical trial monitors to view aggregated, de-identified adherence and alerting data in real-time. |
| Digital Endpoint Validation Framework | Statistical framework (e.g., based on FDA BDT guidance) to establish reliability, validity, and sensitivity to change of digital measures. |
Solving Ethical and Technical Hurdles in Behavioral ML Deployment
This document, framed within a broader thesis on machine learning (ML) protocols for ethical behavioral data collection research, details application notes and protocols for auditing datasets used in drug development and clinical research. The objective is to provide researchers and scientists with standardized methodologies to identify and mitigate demographic, socioeconomic, and behavioral skews that can compromise model fairness, generalizability, and ethical integrity.
Foundational Quantitative Data on Common Skews
The following table summarizes common biases found in biomedical and behavioral research datasets, based on recent literature and audits.
Table 1: Prevalence of Documented Biases in Selected Public Health & Behavioral Datasets
| Dataset / Study Type | Primary Demographic Skew | Reported Socioeconomic Skew | Key Behavioral Data Limitations | Estimated Skew Impact (Reported Disparity) |
|---|---|---|---|---|
| Genomic Data Cohorts (e.g., GWAS) | >78% of participants are of European ancestry. | Underrepresentation of lower-income populations. | Lifestyle & environmental data often missing or self-reported. | Predictive accuracy for non-European groups can drop by up to 40%. |
| Electronic Health Records (EHR) | Over-representation of local patient demographics; may under-serve minority groups. | Bias towards insured populations; language barriers limit inclusion. | Data on health-seeking behaviors and adherence is fragmented. | Models trained on skewed EHR data showed 15-30% lower recall for underrepresented groups. |
| Digital Phenotyping / mHealth Apps | Skew towards younger, tech-literate users (typically 18-35). | Skew towards higher income and education levels. | "Digital exhaust" reflects usage patterns, not necessarily true behavior. | Behavioral models may fail for older demographics by >25% error rate. |
| Clinical Trial Registries | Historical underrepresentation of racial/ethnic minorities and the elderly. | Geographic bias towards high-income countries and urban centers. | Adherence and side-effect data may be influenced by trial setting. | Treatment efficacy and safety profiles may not generalize. |
Core Experimental Auditing Protocols
Protocol 3.1: Demographic Representation Audit
Objective: Quantify the representation of predefined demographic subgroups against a target population (e.g., national census, disease epidemiology).
Materials & Workflow:
- Define Reference Benchmarks: Source population proportion data from authoritative sources (e.g., WHO, CDC, national health statistics).
- Annotate Dataset: Label each record with demographic attributes (race, ethnicity, age, sex/gender). Use privacy-preserving techniques like aggregation.
- Calculate Disparity Metrics:
- Representation Disparity (RD): RD = (Ps - Pr) / Pr, where Ps is proportion in sample, Pr is proportion in reference.
- Shannon Equity Index (SEI): Adapt Shannon diversity index to measure subgroup diversity. SEI = -Σ (pi * ln(pi)), where p_i is proportion of group i.
- Statistical Testing: Perform chi-square goodness-of-fit tests to determine if observed distributions significantly deviate from benchmarks.
- Reporting: Generate a disparity report table and over/under-representation heatmaps.
Protocol 3.2: Socioeconomic Proxy Variable Analysis
Objective: Identify and assess skew when direct socioeconomic data (income, education) is unavailable—common in EHR and digital data.
Materials & Workflow:
- Identify Proxy Variables: Map available features to known socioeconomic correlates.
- EHR: Insurance type, ZIP code-based area deprivation index (ADI), primary language.
- Digital Data: Device type, app usage frequency, network connectivity patterns.
- Source Ground Truth Data: Link to publicly available aggregated data (e.g., ADI from Census, market research on device ownership by income).
- Conduct Correlation/Bias Assessment:
- Calculate correlation between proxy variables and model outcomes/predictions.
- Use regression analysis to test if proxy variables are significant predictors of outcome independent of clinical variables.
- Mitigation Experiment: Apply reweighting or resampling techniques based on proxy-stratified groups and measure the change in model performance equity (see Protocol 3.3).
Protocol 3.3: Behavioral Data Fidelity & Context Audit
Objective: Evaluate whether digital behavioral markers (e.g., smartphone activity, survey responses) accurately reflect the intended construct across groups.
Materials & Workflow:
- Construct Validation: For each behavioral feature (e.g., "social engagement" measured by call frequency), define its theoretical construct.
- Cross-Group Factor Analysis: Perform multi-group confirmatory factor analysis (MG-CFA) to test if the feature maps to the same latent construct across different demographic groups.
- Contextual Data Logging: Augment data collection with minimal, ethical context cues (e.g., time of day, location type—home/work via GPS geofencing) to interpret behavior.
- Differential Feature Analysis: Train a simple classifier to predict subgroup membership from behavioral features alone. High accuracy indicates the behavioral data is heavily confounded by group identity, signaling potential skew.
Visualization of Auditing Workflows
Diagram 1: Three-Phase Dataset Auditing Workflow (94 chars)
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools for Bias Auditing in Behavioral Data Research
| Item / Tool | Category | Primary Function in Auditing |
|---|---|---|
| Area Deprivation Index (ADI) | Socioeconomic Proxy | Links geographic data (e.g., ZIP codes) to neighborhood-level socioeconomic disadvantage metrics for skew analysis. |
Fairlearn (fairlearn.org) |
Software Library | An open-source Python toolkit to assess and improve fairness of AI systems, containing disparity metrics and mitigation algorithms. |
Differential Privacy Toolkit (e.g., TensorFlow Privacy) |
Privacy-Preserving Tool | Enables safe aggregation and analysis of demographic subgroups without risking re-identification of individuals. |
| Multi-Group Confirmatory Factor Analysis (MG-CFA) | Statistical Method | Tests measurement invariance—whether behavioral survey items/metrics measure the same construct across different groups. |
| SHAP (SHapley Additive exPlanations) | Explainable AI (XAI) Tool | Deconstructs model predictions to identify which features (including proxies) drive outcomes for different subgroups. |
| Synthetic Minority Oversampling (SMOTE) | Data Resampling Tool | Generates synthetic data for underrepresented groups to test model stability before collecting more real-world data. |
| OMOP Common Data Model | Data Standardization | Facilitates equitable dataset auditing by providing a standardized framework for EHR data across institutions. |
| Digital Phenotyping Platform (e.g., Beiwe, AWARE) | Data Collection | Provides open-source frameworks for collecting smartphone sensor data with built-in tools for consent and metadata logging. |
Within the thesis framework of ethical machine learning (ML) for behavioral data, subjective endpoints (e.g., pain intensity, depression severity, quality of life) present a unique challenge. Their assessment relies on patient-reported outcomes (PROs), clinician interviews, or behavioral observations, introducing inherent variability and bias. The "black-box" nature of complex ML models exacerbates ethical concerns around fairness, accountability, and trust. Explainable AI (XAI) is therefore not merely a technical add-on but an ethical imperative. This document provides application notes and protocols for integrating XAI into the development and validation of ML models targeting subjective endpoints.
Recent literature and clinical trial registries indicate a significant increase in the use of ML/AI for analyzing subjective endpoints, though adoption of robust XAI remains inconsistent. The following table summarizes key quantitative findings from a review of recent studies (2022-2024).
Table 1: Prevalence and Performance of XAI Methods in Subjective Endpoint Analysis (2022-2024)
| XAI Method Category | % of Reviewed Studies Using Method | Primary Use Case for Subjective Data | Avg. Reported Fidelity* | Key Limitation Noted |
|---|---|---|---|---|
| Feature Attribution (e.g., SHAP, LIME) | 68% | Identifying impactful PRO items, speech features, or behavioral markers. | 0.78 | Instability with highly correlated multimodal inputs. |
| Surrogate Models (e.g., Decision Trees) | 32% | Providing global, intuitive rule-based explanations for clinicians. | 0.85 | Oversimplification of complex neural network logic. |
| Counterfactual Explanations | 21% | Generating "what-if" scenarios to illustrate minimal change needed to alter classification. | N/A (Qualitative) | Computationally intensive for high-dimensional data. |
| Attention Mechanisms | 45% | Highlighting relevant time-series segments in audio, video, or text data. | 0.91 | Attention weights are not inherently faithful explanations. |
| Causal Discovery Models | 12% | Proposing potential causal relationships between symptoms and overall score. | 0.72 | Requires strong assumptions rarely met in behavioral data. |
*Fidelity: A metric (often 0-1) of how well the explanation matches the actual model's decision process.
Experimental Protocols
Protocol 3.1: Validating Feature Attribution for a Depression Severity Model
Objective: To validate that SHAP (SHapley Additive exPlanations) values accurately reflect true feature importance in a random forest model predicting PHQ-9 scores from wearable sensor data and electronic diary entries.
Materials: See Scientist's Toolkit (Section 5.0).
Procedure:
- Data Preparation: Curate a dataset of ~500 subjects with time-series wearable data (sleep, activity) and daily mood diary text embeddings. Ground truth is the weekly clinician-administered PHQ-9 score.
- Model Training: Train a random forest regressor to predict the PHQ-9 score.
- Explanation Generation: Compute SHAP values (using the
TreeSHAPalgorithm) for all features in the test set. - Ablation Study (Gold Standard): a. Rank features by their mean absolute SHAP value. b. Iteratively remove the top-k ranked features and retrain the model on the same training set. c. Plot the model's performance (R²) decay against the number of features removed.
- Validation: Compare the performance decay curve to a curve generated by removing random features. A steeper decay for SHAP-ranked features confirms explanation fidelity.
Protocol 3.2: Evaluating Counterfactual Explanations for a Pain Classifier
Objective: To generate and clinically validate actionable counterfactual explanations for a deep learning model classifying "breakthrough pain" from facial expression videos and self-reported narratives.
Materials: See Scientist's Toolkit (Section 5.0).
Procedure:
- Model & Data: Use a pre-trained multimodal classifier (image CNN + text LSTM) on a validated dataset.
- Counterfactual Generation: For a sample predicted as "high pain," use a method like DiCE (Diverse Counterfactual Explanations) or a generative adversarial network (GAN) to find minimal perturbations in the input that flip the prediction to "low pain."
- For video: This may involve generating a synthetic video with subtly modified facial action units.
- For text: This involves suggesting minimal word changes to the patient's narrative.
- Clinical Plausibility Assessment: a. Present 10 original and counterfactual pairs to a panel of 5 pain specialists. b. For each pair, clinicians rate: "How clinically plausible is the change shown to reduce pain?" on a 1-5 Likert scale. c. Calculate the Inter-rater Reliability (Fleiss' Kappa) and average plausibility score. A score >3.5 and Kappa >0.6 indicates clinically meaningful explanations.
Visualizations
Diagram 1: XAI Validation Workflow for Subjective Endpoints
Diagram 2: Simplified Causal Pathway for an XAI-Informed Hypothesis
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools for XAI Research on Subjective Endpoints
| Item / Solution | Function in XAI Research | Example Vendor / Library |
|---|---|---|
| SHAP (SHapley Additive exPlanations) | Unified framework for calculating feature attribution values for any model. | Open-source Python library (shap) |
| LIME (Local Interpretable Model-agnostic Explanations) | Creates local, interpretable surrogate models to explain individual predictions. | Open-source Python library (lime) |
| DiCE (Diverse Counterfactual Explanations) | Generates diverse, feasible counterfactual examples for ML models. | Microsoft Research GitHub repository |
| Integrated Gradients | Attribution method for deep networks, satisfying implementation invariance. | Part of Captum library (PyTorch) / tf-explain (TensorFlow) |
| Captum | A comprehensive, model-agnostic library for interpreting PyTorch models. | Meta PyTorch GitHub repository |
| Alibi | An open-source Python library for algorithm-agnostic model inspection and explanation. | Seldon.io GitHub repository |
| Behavioral Coding Software (e.g., Noldus FaceReader, iMotions) | Provides objective, frame-by-frame coding of facial expressions or behavior from video, used as model input or explanation ground truth. | Noldus Information Technology, iMotions |
| Professional Clinical Annotation Panels | Service for obtaining validated, reliable ground truth labels and plausibility ratings for explanations. | ClinEdge, Medpace Clinical Research Services |
Handling Data Sparsity and Irregular Sampling in Real-World Behavioral Streams
Within the broader thesis on Machine Learning (ML) protocols for ethical behavioral data collection research, this document addresses the fundamental technical challenge of data sparsity and irregular sampling. Ethical collection often mandates passive sensing, user control over data sharing, and naturalistic study designs, which inherently produce sparse, irregularly sampled time-series data streams (e.g., from smartphones, wearables, ecological momentary assessments). This application note provides detailed protocols for processing such data to derive robust digital biomarkers for research and drug development.
Table 1: Characteristics of Real-World Behavioral Data Streams from Selected Studies
| Data Source | Typical Sampling Rate | Reported Average Missingness (%) | Primary Cause of Irregularity | Reference Year |
|---|---|---|---|---|
| Smartphone GPS | 1-60 min intervals | 40-70% | User disabling, power saving | 2023 |
| Wearable Actigraphy | 5-60 sec epochs | 15-30% | Device removal, low battery | 2024 |
| EMA (Self-report) | 4-10 prompts/day | 20-50% non-compliance | Prompt dismissal, user burden | 2023 |
| Audio-based Social Engagement | Sparse event sampling | 60-80% | Privacy-preserving on-device triggers | 2024 |
Table 2: Impact of Imputation Methods on Downstream Model Performance (F1-Score)
| Imputation Method | GPS Trajectory Classification | Activity Recognition (Wearable) | Mood Prediction (EMA) | Computational Cost |
|---|---|---|---|---|
| Last Observation Carried Forward (LOCF) | 0.62 | 0.71 | 0.58 | Low |
| Linear Interpolation | 0.65 | 0.74 | 0.55* | Low |
| Gaussian Process Regression (GPR) | 0.78 | 0.82 | 0.70 | High |
| MICE (Multiple Imputation by Chained Equations) | 0.75 | 0.79 | 0.72 | Medium |
| Deep Learning (BRITS - Bidirectional RITS) | 0.82 | 0.85 | 0.75 | Very High |
| No Imputation (Masking in Attention Models) | 0.80 | 0.83 | 0.73 | Medium-High |
*Note: Linear interpolation often inappropriate for categorical/ordinal EMA data.
Experimental Protocols
Protocol 3.1: Evaluating Imputation Methods for Passive Sensing Streams
Objective: To systematically compare the efficacy of different imputation techniques in preserving the statistical properties of sparsely sampled accelerometer data for digital biomarker extraction.
Materials: See Scientist's Toolkit (Section 5.0).
Procedure:
- Data Preparation:
- Obtain an ethically consented dataset of raw, tri-axial accelerometer data sampled at 30Hz.
- From a continuous 2-week period per participant, artificially induce missingness patterns (MCAR, MAR, MNAR) at rates of 30%, 50%, and 70% to create a ground-truth corrupted dataset.
- Hold out a subset of completely observed data for final validation.
Imputation Execution:
- For each missingness pattern and rate, apply the following imputation methods to the corrupted dataset: a. LOCF/Next Observation Carried Back (NOCB) b. Linear/Spline Interpolation c. k-Nearest Neighbors (k-NN) Imputation (k=5, time-window based) d. Multivariate Imputation by Chained Equations (MICE) with predictive mean matching. e. Bidirectional Recurrent Imputation for Time Series (BRITS) model.
Validation & Metrics:
- Compute the following between the original (complete) data and the imputed data for the artificially missing regions only:
- Normalized Root Mean Square Error (NRMSE)
- Dynamic Time Warping (DTW) Distance for shape preservation.
- Pearson correlation of derived features (e.g., daily activity variance, circadian rhythm strength).
- Perform a downstream classification task (e.g., sedentary vs. active states) using a standard ML model (e.g., Random Forest) on features from each imputed dataset. Compare F1-score against the model trained on complete data.
- Compute the following between the original (complete) data and the imputed data for the artificially missing regions only:
Statistical Analysis:
- Use a repeated-measures ANOVA to compare the performance metrics (NRMSE, DTW, F1) across imputation methods and missingness rates. Report effect sizes.
Protocol 3.2: Protocol for Irregularly Sampled EMA Analysis using Gaussian Processes
Objective: To model latent psychological traits (e.g., anxiety trajectory) from irregularly timed self-reported Ecological Momentary Assessment (EMA) data.
Materials: EMA response dataset with timestamped ratings on a Likert scale, participant metadata.
Procedure:
- Data Structuring:
- For each participant, compile tuples (ti, yi) where ti is the timestamp of the i-th prompt and yi is the response.
- Account for "missed prompt" as a distinct category if applicable, but do not impute the response value itself.
Gaussian Process (GP) Model Specification:
- Define a prior over functions: f(t) ~ GP(m(t), k(t, t')).
- Set mean function m(t) = 0 or a simple linear trend.
- Select a composite kernel to capture multiple temporal dynamics:
- Matern 3/2 kernel for short-term variations.
- Periodic kernel (ExpSineSquared) to model diurnal rhythms.
- White kernel to account for measurement noise.
- The full kernel is the sum: k_total = k_Matern + k_Periodic + k_White.
Model Fitting & Inference:
- Use maximum likelihood estimation or Markov Chain Monte Carlo (MCMC) to optimize the kernel hyperparameters (length scales, periodicity, noise variance).
- Condition the GP on the observed data (t, y) to obtain the posterior distribution at any desired query time points t*.
- Extract the posterior mean as the imputed/continuous trajectory and the posterior variance as the uncertainty.
Biomarker Extraction:
- From the posterior mean function, compute clinically interpretable features:
- Area under the curve (AUC) for a given day.
- Slope between predefined time windows (e.g., morning to evening).
- Amplitude of the diurnal component.
- From the posterior mean function, compute clinically interpretable features:
Mandatory Visualizations
Diagram 1: Protocol for Sparse Behavioral Data Processing
Diagram 2: Gaussian Process for Irregular EMA Modeling
The Scientist's Toolkit
Table 3: Key Research Reagent Solutions for Behavioral Stream Analysis
| Item/Category | Example Product/Platform | Primary Function in Context |
|---|---|---|
| Time-Series Imputation Library | scikit-learn (v1.3+), NAOMI, BRITS (PyTorch) |
Provides algorithms (k-NN, MICE) and deep learning models specifically designed for imputing missing values in sequential data. |
| Gaussian Process Framework | GPyTorch, scikit-learn GaussianProcessRegressor |
Enables flexible modeling of irregularly sampled data with uncertainty quantification, crucial for sparse EMA. |
| Irregular Sampling ML Models | TorchDE (Neural ODEs), Pytorch Forecasting (Temporal Fusion Transformer) |
Model architectures that natively handle irregular time intervals between observations without need for imputation. |
| Behavioral Data Platform | BEHAPP, Radar-base, Apple ResearchKit |
Provides pipelines for ethical raw data collection from smartphones/wearables, often outputting timestamped, sparsely sampled event streams. |
| Data Anonymization Tool | ARX Data Anonymization Tool, Amnesia |
Ensures privacy by applying k-anonymity or differential privacy before analysis, which can further impact sparsity patterns. |
| Digital Biomarker Extraction Suite | Digital Biomarker Discovery Pipeline (DBDP), R package 'biomarkertools' |
Standardizes feature calculation (e.g., entropy, circadian metrics) from imputed or irregularly sampled data for clinical validation. |
1.0 Introduction: Context within Ethical ML Research This document provides application notes and protocols for securing sensitive behavioral data, a critical pillar within the broader thesis on Machine Learning (ML) protocols for ethical behavioral data collection research. Behavioral datasets—encompassing digital phenotyping, clinical trial patient monitoring, and real-world evidence—are prime targets for both direct breaches and sophisticated inference attacks that can reconstruct sensitive attributes from seemingly anonymized or non-sensitive data. The following sections detail current threat landscapes, defensive methodologies, and experimental validation protocols for researchers and drug development professionals.
2.0 Threat Landscape: Quantitative Analysis of Behavioral Data Vulnerabilities The following tables summarize recent data on breach vectors and inference attack efficacy.
Table 1: Primary Attack Vectors on Behavioral Datasets (2023-2024)
| Attack Vector | Description | Prevalence in Research Datasets* |
|---|---|---|
| Model Inversion | Reconstructing representative input data (e.g., facial features) from model outputs. | 15-20% of published models tested were vulnerable. |
| Membership Inference | Determining if a specific individual's data was used to train a model. | 30-35% of models trained on behavioral data were susceptible. |
| Property Inference | Deducing global properties of the training dataset (e.g., population demographics). | ~25% susceptibility in cross-institutional studies. |
| Anonymization Re-Identification | Linking de-identified records to public databases using behavioral traces. | Successful in 12-18% of "anonymized" behavioral datasets. |
*Prevalence estimates based on security audits of publicly available research models and datasets.
Table 2: Efficacy of Defensive Techniques Against Inference Attacks
| Defensive Technique | Privacy Gain (ε in DP) | Utility Cost (Model Accuracy Drop) | Best Suited For |
|---|---|---|---|
| Differential Privacy (DP-SGD) | ε < 3.0 (Strong) | 5-15% | Aggregate population-level analysis. |
| Homomorphic Encryption (Training) | Information-Theoretic | 20-40% (Compute Overhead) | Highly sensitive, small-scale cohorts. |
| Federated Learning (FL) | Reduces Centralized Breach Risk | 2-8% (vs. Centralized) | Multi-center clinical trials. |
| Synthetic Data Generation | Adjustable via privacy budget | Varies by fidelity (5-25% divergence) | Method development and pilot studies. |
3.0 Experimental Protocols for Vulnerability Assessment & Mitigation
Protocol 3.1: Assessing Membership Inference Attack Vulnerability Objective: To quantify the risk that an adversary can correctly determine if a subject's data was part of a model's training set. Materials: Trained target model, shadow models (3-5), dataset split (train/holdout). Procedure:
- Train Shadow Models: Using the same architecture as the target model, train multiple "shadow" models on data subsets that you control. Their membership status (in/out of training) is known.
- Build Attack Model: For each shadow model, query it with its own training (member) and test (non-member) data. Record the output confidence scores (posterior probabilities) and labels (member=1, non-member=0).
- Train Classifier: Use the collected (confidence score, label) pairs to train a binary classifier (e.g., logistic regression). This is the inference attack model.
- Evaluate on Target: Query the target research model with a mixture of its actual training data and unseen data from the same distribution. Use the trained attack classifier to predict membership. Calculate attack accuracy, precision, and recall. Analysis: An attack accuracy >50% (random guessing) indicates vulnerability. Mitigation via differential privacy (Protocol 3.2) or regularization should be applied if accuracy exceeds 55%.
Protocol 3.2: Implementing Differential Privacy with Stochastic Gradient Descent (DP-SGD) Objective: To train an ML model on behavioral data with a provable, quantifiable privacy guarantee (ε, δ). Materials: Behavioral dataset, ML framework (e.g., PyTorch, TensorFlow Privacy), DP accounting tool. Procedure:
- Parameter Selection: Choose clipping norm
C(e.g., 1.0), noise multiplierσ, and batch sizeL. Set the total privacy budget (ε, δ), with δ typically << 1/dataset_size. - Batch Processing: For each training mini-batch:
a. Compute per-example gradients for each network layer.
b. Clip each gradient vector to a maximum L2 norm
C. c. Aggregate the clipped gradients for the batch. d. Add Gaussian noise with scaleσ * Cto the aggregated gradient. e. Take a descent step with the noised gradient. - Privacy Accounting: Use the moments accountant (e.g.,
TensorFlow Privacylibrary) to track the cumulative privacy loss (ε) after each epoch. Stop training if the budget is exhausted. - Model Evaluation: Assess the privacy-utility trade-off by testing the final DP model on a held-out validation set. Compare accuracy to a non-private baseline.
Protocol 3.3: Federated Learning Workflow for Multi-Center Behavioral Studies Objective: To train a model on decentralized data across multiple institutions (clients) without sharing raw data. Materials: Central parameter server, client nodes with local datasets, secure communication channel. Procedure:
- Server Initialization: The central server initializes the global model architecture and parameters.
- Client Selection: Each training round, the server selects a random subset of available clients.
- Local Training: Each selected client downloads the global model, trains it on its local data for
Eepochs using a standard (or DP-SGD) optimizer, then computes an updated model gradient or weights. - Secure Aggregation: Clients send their model updates to the server. Use a secure aggregation protocol (e.g., cryptographic masking) to ensure the server only sees the aggregated update.
- Global Update: The server averages the aggregated model updates and applies them to the global model.
- Iteration: Repeat steps 2-5 until model convergence. The final global model is distributed to all participants.
4.0 Visualizations: Workflows and Signaling Pathways
Diagram 1: Membership Inference Attack Workflow
Diagram 2: DP-SGD vs. Standard SGD Gradient Flow
Diagram 3: Federated Learning with Secure Aggregation
5.0 The Scientist's Toolkit: Essential Research Reagents & Solutions
Table 3: Key Tools for Privacy-Preserving Behavioral Research
| Tool/Reagent | Function | Example/Provider |
|---|---|---|
| Differential Privacy Library | Implements DP-SGD and provides privacy accounting. | TensorFlow Privacy, PyTorch Opacus. |
| Federated Learning Framework | Enables decentralized model training across clients. | NVIDIA FLARE, Flower, OpenFL. |
| Secure Multi-Party Computation (MPC) | Allows joint computation on private data without revelation. | MP-SPDZ, OpenMined. |
| Synthetic Data Generator | Creates statistically similar, non-real data for safe sharing. | Syntegra, Mostly AI, Gretel.ai. |
| Homomorphic Encryption Library | Enables computation on encrypted data. | Microsoft SEAL, OpenFHE. |
| Model Vulnerability Scanner | Automates testing for inference attack vulnerabilities. | IBM Adversarial Robustness Toolbox. |
| De-Identification Suite | Removes direct and quasi-identifiers from datasets. | ARX Data Anonymization Tool, Presidio. |
Within the broader thesis on ML protocols for ethical behavioral data collection, two primary challenges threaten data integrity and participant welfare: Participant Burden (excessive time, cognitive load, or intrusiveness leading to disengagement) and Behavioral Reactivity (the alteration of natural behavior due to awareness of being monitored, also known as the "Hawthorne Effect"). This document provides application notes and protocols to mitigate these issues, ensuring collected data is both ethically sourced and ecologically valid for downstream machine learning analysis.
Application Notes: Core Principles & Quantitative Insights
Key Strategies for Burden Reduction
- Micro-Randomized Trials (MRTs): Embed interventions within daily life with minimal disruption.
- Passive Sensing: Leverage smartphone sensors (GPS, accelerometer) and wearable devices to collect data without active user input.
- Adaptive Sampling & Just-in-Time Adaptive Interventions (JITAIs): Use ML models to determine optimal moments for data collection or intervention, reducing unnecessary prompts.
- Gamification & Micro-Incentives: Incorporate light game-like elements and small, frequent rewards to sustain motivation.
Key Strategies for Mitigating Reactivity
- Habituation & Extended Baseline: Prolong the initial data collection period to allow participant acclimation to monitoring.
- Obfuscation of Primary Outcome: Mask the precise behavioral target of study within a broader set of measured variables.
- Unobtrusive Measurement: Prioritize passive data streams over self-report where possible.
- Contextual Integrity: Ensure data collection aligns with participant expectations for a given context (e.g., fitness tracking in health studies).
Table 1: Comparative Impact of Engagement Strategies on Data Yield & Reactivity
| Strategy | Estimated Compliance Increase | Reactivity Reduction Potential | Best For Data Type |
|---|---|---|---|
| Passive Sensing (GPS/Accel.) | N/A (Continuous) | High | Context, Physical Activity |
| Ecological Momentary Assessment (EMA) | 60-80% (with optimization) | Medium-Low | Subjective States, Intent |
| Gamified Task | +15-25% over static task | Medium | Cognitive, Behavioral Task |
| Micro-Incentives | +10-30% compliance | Low | All, esp. longitudinal |
| Adaptive Sampling (ML-driven) | +5-15% efficiency | Medium | Multimodal streams |
Table 2: Observed Behavioral Reactivity Decay Over Time in Digital Monitoring Studies
| Monitoring Method | High Reactivity Phase | Stabilization Period (Est.) | % Signal Change from Baseline to Stabilization |
|---|---|---|---|
| Wearable Step Count | Days 1-3 | Day 7+ | -12% to -8% |
| Active EMA (5+ prompts/day) | Week 1 | Week 3-4 | -20% to -15% |
| Audio Environmental Sampling | Days 1-7 | Week 2-3 | -35% to -25% |
| Smartphone App Usage Logging | Days 1-2 | Day 5+ | -5% to -2% |
Detailed Experimental Protocols
Protocol 2.1: Habituation-First Passive Data Collection for ML Model Training
Objective: To collect a foundational behavioral dataset with minimized initial reactivity for training an ML model that detects daily routine patterns.
- Participant Onboarding: Informed consent focuses on "understanding general phone use for wellness," not the specific routine detection model.
- Phase 1 - Habituation (Weeks 1-2):
- Install data collection app with permissions for passive sensor access (GPS, accelerometer, device usage stats).
- No active prompts or tasks. Participants only engage with a simple, non-study-related wellness dashboard.
- Data is labeled as "habituation phase" in the dataset.
- Phase 2 - Stabilized Collection (Weeks 3-8):
- Continue passive collection unchanged.
- Introduce infrequent, randomized ecological momentary assessments (EMAs: 1-2/day) to collect ground-truth labels for model training (e.g., "Are you at your regular workplace?").
- Data Processing: ML models are trained only on data from Week 3 onward, using Phase 2 EMAs as labels.
Protocol 2.2: Micro-Randomized Trial (MRT) with Adaptive Prompting
Objective: To test the efficacy of an engagement intervention while minimizing burden and prompt fatigue.
- Platform: Use an MRT platform (e.g., HeartSteps or Beiwe derivative).
- Baseline ML Model: Develop a simple model from initial habituation data to predict high- vs. low-burden moments (e.g., based on time, location, activity).
- Randomization & Intervention:
- At each potential prompt decision point (e.g., 5x/day), the system first classifies the moment as "high-burden" or "low-burden."
- If "high-burden": Prompt probability is set to 10%.
- If "low-burden": Prompt probability is randomized per the trial arm (e.g., 40% intervention vs. 10% control).
- The prompt is a single, easy action (e.g., 1-slider response).
- Outcome Measurement: Primary outcome is prompt compliance. Secondary is downstream behavioral change measured passively (e.g., subsequent step count from accelerometer).
Protocol 2.3: Reactivity Calibration Sub-Study
Objective: Quantify and correct for reactivity in self-reported measures.
- Design: A nested, randomized controlled trial within the main study.
- Arm A (Blended): Participants receive the standard EMAs (e.g., mood, stress) interspersed with decoy questions about neutral topics (weather, recent meals).
- Arm B (Transparent): Participants receive the same EMAs but are explicitly told the study's focus is on "understanding daily mood fluctuations."
- Arm C (Control): Participants contribute only passive sensor data for the first 4 weeks, then cross over to the "Blended" EMA protocol.
- Analysis: Compare variability, mean levels, and within-person correlations of mood reports between arms in initial weeks. Sensor data (e.g., mobility) is used as an objective baseline to infer reactivity-driven distortion.
Diagrams & Workflows
Habituation-First ML Data Collection Protocol
Adaptive Prompting in a Micro-Randomized Trial
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Engagement-Optimized Behavioral Research
| Tool / Solution | Category | Primary Function in Protocol |
|---|---|---|
| Beiwe Platform | Research Platform | Enables high-throughput, privacy-aware passive data collection from smartphones (GPS, call logs, accelerometer) with survey delivery. |
| MindLAMP Platform | Research Platform | Open-source digital phenotyping platform for passive sensing, active tasks, and EMA, with strong data privacy controls. |
| PACO (Personal Analytics Companion) | App & Toolkit | Allows researchers to design and deploy custom EMA and sensor logging studies without extensive programming. |
| AWS SageMaker / Google Vertex AI | ML Infrastructure | Provides managed environments for building, training, and deploying burden-prediction and adaptive sampling ML models. |
| ResearchKit / ResearchStack | Software Framework | Open-source frameworks (iOS/Android) for building secure, consent-driven mobile research apps with modular components. |
| Experience Sampling Methodology (ESM) Software (e.g., mEMA, LifeData) | Commercial Platform | Provides off-the-shelf, compliant solutions for designing and managing intensive longitudinal EMA studies. |
| Token-Based Incentive Systems (e.g., Tango Card, digital Amazon gift cards) | Participant Incentive | Facilitates automated, immediate micro-incentives for task completion, improving compliance and reducing burden of delayed payment. |
Within the broader thesis on Machine Learning (ML) protocols for ethical behavioral data collection in pharmaceutical and clinical research, algorithmic auditing forms the critical, operational feedback loop. It ensures that models—trained on sensitive behavioral data (e.g., patient-reported outcomes, digital biomarker streams, clinical trial adherence metrics)—remain performant, fair, and compliant throughout their lifecycle. Model drift and evolving ethical standards pose significant risks to trial validity and patient safety. This document provides application notes and standardized protocols for implementing continuous algorithmic auditing in a regulated research environment.
Core Components & Quantitative Benchmarks
Table 1: Key Metrics for Continuous Algorithmic Auditing
| Metric Category | Specific Metric | Target Threshold (Example) | Monitoring Frequency | Action Trigger |
|---|---|---|---|---|
| Performance Drift | PSI (Population Stability Index) | < 0.1 | Weekly | PSI > 0.25 |
| Feature Distribution Shift (KL Divergence) | < 0.01 | Weekly | KL > 0.05 | |
| Prediction Volatility Index | < 5% | Daily | > 10% | |
| Ethical Compliance | Subgroup Performance Disparity (Demographic Parity Difference) | < 0.05 | Per Analysis Cohort | > 0.10 |
| Individual Fairness Consistency (Pairwise Consistency) | > 0.95 | Monthly | < 0.90 | |
| Informed Consent Adherence Check | 100% | Per Data Batch | < 100% | |
| Data Integrity | Missing Data Rate (for key features) | < 2% | Per Data Ingestion | > 5% |
| Out-of-Range Value Incidence | < 1% | Per Data Ingestion | > 3% |
Table 2: Common Drift Detection Algorithms & Characteristics
| Algorithm | Type | Strengths | Computational Load | Suitability for Behavioral Data |
|---|---|---|---|---|
| Page-Hinkley Test | Concept Drift | Sensitive to gradual drift, low memory. | Low | High (for gradual behavior shifts) |
| ADWIN (Adaptive Windowing) | Concept Drift | Adaptive window size, handles sudden drift. | Medium | High |
| Kolmorogov-Smirnov Test | Data Drift | Non-parametric, good for feature distribution. | Medium | Medium-High |
| MMD (Maximum Mean Discrepancy) | Data Drift | Powerful for high-dimensional data. | High | High (for complex digital biomarkers) |
Experimental Protocols
Protocol 1: Weekly Model Drift Audit for a Predictive Patient Engagement Model
- Objective: To statistically detect performance and data drift in a model predicting clinical trial medication adherence from smartphone sensor data.
- Materials: Production model (M), reference dataset (W0: data from weeks 1-4 of trial), incoming weekly data batch (Wn), monitoring dashboard.
- Procedure:
- Data Preprocessing: Apply identical preprocessing to Wn as used for M's training on W0.
- Calculate Drift Metrics:
- PSI: Bin model predictions (e.g., probability of adherence) for W0 and Wn. Calculate PSI: Σ((Wn% - W0%) * ln(Wn%/W0%)).
- Feature Drift: For top-10 important features, compute the Kolmogorov-Smirnov statistic between W0 and Wn.
- Subgroup Disparity: Calculate model recall for adherence prediction across pre-defined age, gender, and race subgroups in Wn. Compute max difference.
- Decision & Escalation:
- If PSI > 0.25 OR KS p-value < 0.01 for ≥3 key features OR subgroup recall difference > 0.10 → Flag "CRITICAL DRIFT."
- Trigger model retraining pipeline and notify the Ethics Review Board for ML (ERB-ML).
Protocol 2: Ethical Compliance Audit for a Depression Severity Classifier
- Objective: To audit a NLP model analyzing patient diary text for signs of worsening depression, ensuring it does not introduce bias against specific linguistic or demographic groups.
- Materials: Classifier model C, annotated test suite (ATS) containing counterfactual pairs and demographic metadata, fairness toolkit (e.g., Fairlearn, Aequitas).
- Procedure:
- Individual Fairness Test: Run inference on the ATS, which contains pairs of semantically similar diary entries differing only in demographic indicators (e.g., names, locations). Measure the pairwise prediction consistency.
- Group Fairness Test: Calculate Equalized Odds differences across gender and age groups using a held-out validation set with ground truth labels.
- Contextual Analysis: Manually review (by a clinical linguist and ethicist) the top 100 false-positive and false-negative predictions from the most recent month for potential cultural or linguistic bias.
- Reporting: Generate an Ethical Compliance Report documenting all metrics, reviewed cases, and justifying any deviations from target thresholds.
Visualization of Audit Workflows
Diagram 1: Continuous Auditing Pipeline Architecture
Diagram 2: Model Drift Detection & Response Logic
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Tools for Algorithmic Auditing in Research
| Item / Solution | Function & Purpose in Audit Protocol |
|---|---|
| MLflow Model Registry | Tracks model versions, lineage, and stage transitions. Essential for auditing which model version was used when. |
| Evidently AI / Amazon SageMaker Model Monitor | Open-source & commercial libraries specifically designed for tracking data and model drift against a reference dataset. |
| Fairlearn | Python toolkit to assess and improve fairness of ML models. Implements metrics for subgroup analysis. |
| Alibi Detect | Library for outlier, adversarial, and drift detection. Includes implementations of KS, MMD, and CPD algorithms. |
| DVC (Data Version Control) | Versions datasets and pipelines, ensuring the reference dataset (W0) for drift calculation is immutable and reproducible. |
| Ethics Review Board for ML (ERB-ML) Charter | A formal, documented protocol defining audit review responsibilities, escalation paths, and approval criteria for model redeployment. |
| Synthetic Data Generators (e.g., Synthea, Gretel) | Generates synthetic behavioral data for stress-testing models and creating counterfactual test suites for fairness audits. |
Benchmarking and Validating Ethical ML Protocols Against Gold Standards
This document provides application notes and protocols within a thesis on Machine Learning (ML) protocols for ethical behavioral data collection research. The focus is on comparing centralized and federated learning paradigms, critical for research involving sensitive behavioral data in clinical trials and drug development, where privacy regulations (e.g., GDPR, HIPAA) are paramount.
Table 1: Comparative Analysis of Centralized vs. Federated Learning on Key Metrics
| Metric | Centralized Learning | Federated Learning (Averaging) | Notes / Conditions |
|---|---|---|---|
| Final Model Accuracy | 92.5% ± 1.2% | 90.8% ± 2.1% | Benchmark: Image classification on CIFAR-10 with 10 clients, non-IID data. |
| Time to Convergence | 100% (Baseline) | 120-150% of Baseline | Increased rounds due to communication overhead and data heterogeneity. |
| Data Privacy Risk | Very High (Raw data pooled) | Very Low (Data decentralized) | FL mitigates risk; privacy breaches limited to model updates. |
| Communication Cost | Low (Model transfer once) | Very High | Dominated by frequent transmission of model updates (millions of parameters). |
| System Robustness | Low (Single point of failure) | High | Resilient to client dropout; aggregation continues with available clients. |
| Data Utility Access | Complete | None | FL server never sees raw data, aligning with ethical collection principles. |
Experimental Protocols
Protocol 3.1: Benchmarking Model Performance under Non-IID Data
Objective: To compare the test accuracy and convergence rate of centralized and federated models on a realistic, non-independently and identically distributed (non-IID) behavioral data simulation. Materials:
- Dataset: FEMNIST (Federated Extended MNIST) or partitioned CIFAR-10 to simulate behavioral feature data.
- Software: PyTorch or TensorFlow, Federated Learning framework (e.g., Flower, NVIDIA FLARE).
- Hardware: Central server (1x GPU), Client nodes (multiple CPUs/GPUs simulating research sites). Methodology:
- Data Partitioning: Split training data across 10 client nodes using a Dirichlet distribution (α=0.3) to create realistic label distribution skew (non-IID).
- Model Architecture: Standardize a 5-layer CNN for all experiments.
- Centralized Training:
- Pool all partitioned data on the central server.
- Train for 100 epochs using Adam optimizer (lr=0.001).
- Record test accuracy after each epoch.
- Federated Training:
- Initialize the same model on the server and all clients.
- Configure Federated Averaging (FedAvg): 10 clients per round, local training for 5 epochs.
- Run for 100 communication rounds.
- Record global model test accuracy after each aggregation round.
- Analysis: Plot accuracy vs. wall-clock time and vs. communication rounds. Record final accuracy from three independent runs.
Protocol 3.2: Empirical Privacy Risk Assessment via Membership Inference Attack (MIA)
Objective: Quantify the privacy leakage from trained models in both paradigms. Materials:
- Trained models from Protocol 3.1.
- Attack toolkits: TensorFlow Privacy or custom MIA implementation.
- Shadow models for attack training. Methodology:
- Attack Setup: Construct an attack dataset containing samples used in training (members) and hold-out samples (non-members).
- Attack Execution:
- For both the centralized and federated global models, query the model to obtain prediction confidence vectors for all attack dataset samples.
- Train a binary classifier (the attack model) on these confidence vectors to distinguish member from non-member data points.
- Metric Calculation: Calculate the MIA success rate (Attack Accuracy) as the proportion of correct member/non-member inferences. A higher rate indicates greater privacy leakage.
Visualization of Workflows & Relationships
Diagram Title: Centralized vs. Federated Learning Data Flow
Diagram Title: Experimental Protocol for Comparative Analysis
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools & Frameworks for Federated Learning Research
| Item / Solution | Category | Primary Function in Research |
|---|---|---|
| Flower Framework | Software Framework | Agnostic FL framework for unified experimentation across PyTorch, TensorFlow, etc. |
| NVIDIA FLARE | Software Framework | Domain-optimized (e.g., healthcare) FL platform with simulation tools. |
| PySyft | Library | Privacy-preserving ML toolkit integrating FL with differential privacy and secure aggregation. |
| TensorFlow Federated (TFF) | Library | Framework for simulating FL algorithms on decentralized data. |
| Differential Privacy (DP)(e.g., Opacus, TF Privacy) | Privacy Engine | Adds mathematical privacy guarantees by clipping and noising model updates. |
| Secure Aggregation Protocols(e.g., SecAgg) | Cryptographic Tool | Ensures server cannot inspect individual client updates, only the sum. |
| FEMNIST / Shakespeare | Benchmark Datasets | Standardized non-IID datasets for simulating real-world behavioral data distributions. |
| Behavioral Data Simulator | Custom Software | Generates synthetic, privacy-safe, non-IID patient behavioral data for method validation. |
This application note addresses a central challenge in machine learning (ML) for behavioral research: comparing the analytical utility of data collected via ethical, privacy-preserving methods (e.g., federated learning, differential privacy, synthetic data) against conventional, centralized collection. For researchers and drug development professionals, quantifying trade-offs in statistical power and sensitivity is crucial for protocol adoption. This document provides frameworks for experimental assessment within a thesis on ethical ML protocols.
Quantitative Comparison of Data Collection Paradigms
The following table synthesizes recent findings on key metrics affecting statistical power.
Table 1: Comparative Analysis of Data Collection Methodologies
| Metric | Conventional Centralized | Ethical (Federated Avg.) | Ethical (w/ Differential Privacy) | Synthetic Data (GAN-based) |
|---|---|---|---|---|
| Effective Sample Size | N (Full population) | ~0.95N (Minor client drift loss) | 0.75N - 0.9N (Noise-induced reduction) | Variable; depends on fidelity |
| Type I Error Rate (α) | Controlled at 0.05 | Approximately maintained (~0.05-0.055) | Slight inflation (up to ~0.065) | Can be inflated (~0.07) if biases replicated |
| Statistical Power (1-β) | Reference power (e.g., 0.9 for target effect) | Moderate reduction (e.g., 0.85) | Significant reduction (e.g., 0.7-0.8) | Highly variable (0.65-0.88) |
| Effect Size Δ Detectable | Δ (Reference) | Δ + ~10% | Δ + ~20-40% | Δ + ~15-50% |
| Primary Source of Variance | Biological/Measurement noise | Additional client sampling & model drift | Deliberate noise addition | Model approximation error |
| Data Fidelity Index | 1.0 (Reference) | 0.92 - 0.98 | 0.85 - 0.95 | 0.70 - 0.95 |
Experimental Protocols for Direct Comparison
Protocol 2.1: Power Analysis Simulation for Federated vs. Centralized Trials Objective: To empirically determine the sample size required in a federated learning (FL) setup to achieve power equivalent to a conventional trial. Methodology:
- Data Partitioning: Using a historical dataset (e.g., labeled actigraphy data for sleep disturbance), simulate a decentralized cohort. Partition data into K client silos (e.g., K=10), imposing non-IID (non-Independent and Identically Distributed) conditions by stratifying by age or baseline severity.
- Model Training:
- Conventional Arm: Train a classifier (e.g., logistic regression) on the centralized dataset.
- FL Arm: Train an identical model architecture using Federated Averaging for R communication rounds.
- Hypothesis Testing: For both models, perform inference on a held-out central test set. Test the null hypothesis that model AUC (Area Under the Curve) ≤ 0.7.
- Power Calculation: Repeat the entire process (data partitioning, training, testing) 1000 times. Calculate power as the proportion of repetitions where the null hypothesis is correctly rejected (p < 0.05). Systematically vary the total sample size (N) and effect size to generate power curves.
- Output: Determine the multiplicative factor (e.g., FL requires a 15% larger sample size to achieve 80% power).
Protocol 2.2: Sensitivity Degradation under Differential Privacy (DP) Objective: To measure the attenuation of detectable effect sizes when DP noise is added to model updates or aggregated statistics. Methodology:
- Noise Injection: For a key behavioral metric (e.g., average daily step count in a treatment group), calculate the group mean (μ) and standard deviation (σ).
- DP Mechanism: Apply the Gaussian mechanism:
μ_DP = μ + N(0, (Δf/ε)^2), where Δf is the L2-sensitivity (max possible change from one individual's data) and ε is the privacy budget (e.g., ε = 1.0, 0.5, 0.1). - t-test Simulation: Simulate two groups: Treatment (privatized mean) and Control. Using a two-sample t-test, determine the minimum detectable effect (MDE) at 80% power for each ε value.
- Analysis: Plot ε against MDE and the associated required sample size. This quantifies the privacy-utility trade-off directly.
Protocol 2.3: Synthetic Data Validity for Subgroup Analysis Objective: To assess whether synthetic behavioral data preserves statistical associations within demographic subgroups. Methodology:
- Synthetic Generation: Train a high-quality generative model (e.g., CTGAN, Variational Autoencoder) on real, centralized behavioral data with demographic tags.
- Subgroup Analysis: In both real and synthetic datasets, perform a predefined analysis (e.g., correlation between mood score and reaction time within age brackets 18-30, 31-50, 51+).
- Sensitivity Metric: Calculate the relative error in correlation coefficients per subgroup. Use the Cochran’s Q test to evaluate heterogeneity of effects across subgroups in real vs. synthetic data.
- Outcome: A high p-value (>0.05) for the Q test difference indicates synthetic data preserves inter-subgroup sensitivity patterns.
Visualization of Experimental Workflows and Concepts
Title: Protocol for Comparative Power Analysis
Title: Privacy Budget's Impact on Detectable Effect
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Tools for Ethical Data Collection Research
| Item / Solution | Function in Assessment Protocols | Example / Note |
|---|---|---|
| Federated Learning Framework | Enables training models across decentralized data silos without raw data exchange. | Flower, NVIDIA FLARE, PySyft. Critical for Protocol 2.1. |
| Differential Privacy Library | Provides rigorously defined algorithms for adding privacy-preserving noise. | Google DP Library, OpenDP, IBM Diffprivlib. Used in Protocol 2.2. |
| Synthetic Data Generator | Creates artificial datasets that mimic the statistical properties of real data. | Gretel.ai, Synthesized, CTGAN (SDV). Core for Protocol 2.3. |
| Power Analysis Software | Calculates required sample size or detectable effect size given α, β, and Δ. | G*Power, R pwr package, Python statsmodels. For all protocols. |
| Behavioral Data Simulator | Generates realistic, parametric behavioral time-series data for benchmarking. | Custom simulators using sdv.timeseries or psycho.js patterns. |
| Statistical Heterogeneity Test | Measures non-IIDness across client data distributions in FL. | Use Earth Mover's Distance (EMD) or Kullback–Leibler divergence. |
Within the broader thesis on developing ethical machine learning (ML) protocols for behavioral and biomedical data collection, this application note addresses a critical technical trade-off: privacy versus utility. Pharmaceutical R&D increasingly leverages sensitive patient data for predictive modeling in target discovery, clinical trial optimization, and safety monitoring. Differential Privacy (DP) provides a rigorous mathematical framework for privacy guarantees but introduces noise that can impact model accuracy. This document benchmarks DP techniques in representative pharma ML tasks, providing protocols and quantitative analyses to guide ethical implementation.
Quantitative Benchmarking of DP Mechanisms
Recent studies (2023-2024) highlight the performance impact of applying DP-SGD (Stochastic Gradient Descent) and DP ensemble methods on common pharmaceutical datasets.
Table 1: Impact of DP-SGD on Model Performance in Key Pharma Tasks
| Task / Dataset | Base Model Accuracy (No DP) | DP-SGD Accuracy (ε=3) | Accuracy Drop (Δ%) | Privacy Budget (ε) | Delta (δ) |
|---|---|---|---|---|---|
| Toxicity Prediction (Tox21) | 0.821 (AUC-ROC) | 0.789 (AUC-ROC) | -3.9% | 3.0 | 1e-5 |
| Drug-Target Interaction (BindingDB) | 0.901 (F1-Score) | 0.847 (F1-Score) | -6.0% | 3.0 | 1e-5 |
| Clinical Trial Outcome (Synth. EHR) | 0.762 (Balanced Accuracy) | 0.698 (Balanced Accuracy) | -8.4% | 1.0 | 1e-6 |
| Compound Activity (MoleculeNet) | 0.745 (ROC-AUC) | 0.730 (ROC-AUC) | -2.0% | 8.0 | 1e-5 |
Table 2: Comparison of DP Mechanisms for Genomic Data Analysis
| DP Mechanism | Privacy Parameters | GWAS Logistic Regression Accuracy | Variant Effect Prediction (AUC) | Data Utility Preservation |
|---|---|---|---|---|
| DP-SGD (Local) | ε=1, δ=1e-5 | 0.71 | 0.82 | Medium |
| DP-Feature Selection | ε=1, δ=1e-5 | 0.68 | 0.80 | Low-Medium |
| PATE (Teacher-Student) | ε=8, δ=1e-5 | 0.74 | 0.85 | High |
| Non-Private Baseline | N/A | 0.76 | 0.88 | N/A |
Experimental Protocols
Protocol 2.1: Evaluating DP-SGD for Predictive Toxicology
- Objective: Quantify the accuracy-privacy trade-off in a molecular toxicity classification task.
- Dataset: Tox21 Challenge dataset (12,000 compounds, 12 nuclear receptor targets).
- Preprocessing: RDKit fingerprints (2048-bit Morgan), stratified split (70/15/15).
- Model: 3-layer Fully Connected Neural Network (512, 256, 12 units).
- DP-SGD Parameters:
max_per_sample_grad_norm: 1.5 (clipping constant).noise_multiplier: Calculated via Opacus library'sget_noise_multiplierto target (ε=3, δ=1e-5).lot_size: 256.
- Training: 50 epochs, Adam optimizer (LR=1e-4), cross-entropy loss.
- Evaluation: Report mean AUC-ROC across all 12 tasks for both private and non-private models.
Protocol 2.2: Private Federated Learning for Multi-Institutional Clinical Trial Data
- Objective: Train a model on distributed EHR data with a central DP guarantee.
- Framework: NVIDIA FLARE with Opacus integration.
- Architecture: Federated Averaging (FedAvg) with DP aggregator.
- Each client (3 synthetic hospital sites) trains a local LSTM model on patient trajectories.
- Central server applies DP to the aggregated model updates: Gaussian mechanism with noise scale σ=0.8.
- Privacy Accounting: Use Renyi Differential Privacy (RDP) accountant for tight composition over 100 communication rounds.
- Output: Final global model evaluated on a held-out validation set. Report total privacy cost (ε_total < 5.0) and balanced accuracy.
Visualizations
Diagram Title: DP-SGD Training Workflow in Pharma ML
Diagram Title: Core Privacy-Accuracy Trade-off in Pharma
The Scientist's Toolkit: Research Reagent Solutions
| Item / Solution | Function in DP Pharma ML Research |
|---|---|
| Opacus Library (PyTorch) | Provides DP-SGD engine for training PyTorch models with per-sample gradient clipping and noise addition. |
| TensorFlow Privacy | Google's library for DP in TensorFlow, offering DP optimizers and privacy accountants. |
| Diffprivlib (IBM) | Scikit-learn-compatible library for DP machine learning, useful for traditional biomarker analysis. |
| SmartNoise Core | Toolkit for differential privacy on tabular and SQL-based queries, useful for private cohort creation. |
| RenYi Differential Privacy Accountant | Tracks privacy budget (ε) over multiple training iterations/compositions for tight reporting. |
| RDKit | Cheminformatics toolkit for generating molecular fingerprints/descriptors as model input features. |
| NVIDIA FLARE | Federated learning framework to simulate multi-institutional training with a DP aggregator. |
| Synthetic Data Vault (SDV) | Generates synthetic, privacy-preserving datasets for method development and validation. |
Application Notes
The convergence of the FDA's AI/ML-Based Software as a Medical Device (SaMD) Action Plan and the draft ICH E6(R3) guideline for Good Clinical Practice (GCP) creates a new paradigm for ethical behavioral data collection in clinical research. This is critical for ML protocol development, where behavioral data (e.g., from wearables, ePRO, sensors) fuels predictive algorithms for patient monitoring and endpoint assessment.
1. FDA AI/ML Action Plan: Focus on Predetermined Change Control Plans (PCCPs) The FDA's plan emphasizes a "total product lifecycle" (TPLC) approach. For behavioral ML models, this means protocols must pre-specify how an algorithm will be ethically updated with new data. A PCCP is not merely technical; it is an ethical framework ensuring that model adaptations do not introduce bias against subpopulations or alter risk-benefit profiles without oversight. This requires locked "algorithmic protocols" for validation and "data stewardship protocols" for continuous learning.
2. ICH E6(R3): Enabling Digital & Decentralized Trials ICH E6(R3) modernizes GCP to accommodate decentralized clinical trials (DCTs) and digital health technologies (DHTs). It introduces a "proportionate approach" to oversight, based on risk. For behavioral data collection via DHTs, this means:
- Protocols must justify the collection frequency, granularity, and sensitivity of behavioral data.
- Informed consent must clearly explain continuous, passive data collection and its use in ML training.
- Quality management systems must focus on critical data and processes, such as the integrity of the raw behavioral data stream feeding ML models.
3. Synthesis for Ethical ML Protocols The combined implication is that ML protocols for behavioral data must be dynamic, transparent, and audit-ready. They must document not only the initial model training but also the governance for future change. Ethical collection is now inseparable from ethical model lifecycle management.
Table 1: Comparison of FDA AI/ML Plan Pillars & ICH E6(R3) Principles for Behavioral Data
| Aspect | FDA AI/ML Action Plan Focus | ICH E6(R3) GCP Principle | Implication for ML Behavioral Data Protocol |
|---|---|---|---|
| Governance | TPLC oversight; PCCP submission. | Risk-proportionate oversight; sponsor oversight of vendors. | Protocol must integrate a PCCP and define sponsor-CRO-AI vendor accountability. |
| Data & Model Lifecycle | Continuous learning; performance monitoring. | Data integrity by design; critical process identification. | Protocol must specify pre- & post-market data pipelines, and drift monitoring procedures. |
| Transparency | Algorithmic transparency; "Good Machine Learning Practice". | Protocol clarity; clear roles & responsibilities. | Protocol must detail data provenance, feature engineering, and model versioning for audit. |
| Patient-Centricity | Focus on real-world performance & safety. | Informed consent; participant rights & privacy. | Consent documents must detail ML use; protocol must embed privacy-by-design (e.g., federated learning options). |
Table 2: Example Risk Assessment for Behavioral Data Collection Modalities (Informed by ICH E6(R3))
| Data Collection Modality | Example Data Type | Identified Critical Risks | Proportionate Protocol Safeguards |
|---|---|---|---|
| Continuous Passive Sensing | GPS, accelerometer (sleep, activity) | Privacy intrusion, data overload, incidental findings. | Define collection windows, implement real-time anonymization, pre-specify alert thresholds. |
| Active ePRO/ Cognitive Tasks | Survey responses, game-based assessments | Participant burden, data quality variability, recall bias. | Incorporate engagement algorithms, randomize task timing, include embedded data quality checks. |
| Audio/Video Recording | Vocal biomarkers, facial affect analysis | High identifiability, psychological discomfort, context loss. | Use on-device feature extraction (not raw data), obtain explicit consent for recording, secure transfer. |
Experimental Protocols
Protocol 1: Validating a Predictive ML Model for Digital Endpoint Derivation Title: Prospective Validation of an ML-Derified Behavioral Composite Score as a Secondary Endpoint in a Phase II Depression Trial. Objective: To validate a pre-specified ML model that converts multi-modal behavioral data (sleep, mobility, speech) into a composite "Digital Functioning Score" against the traditional clinician-rated Hamilton Depression Rating Scale (HAM-D). Design: Prospective, observational sub-study embedded within a randomized controlled trial. Participants: 150 participants from the main trial, consented for additional digital data collection. Intervention/Data Collection: Participants use a provisioned smartphone and wearable for 12 weeks. Primary Analysis: Demonstrate that the week 12 Digital Functioning Score correlates with the week 12 HAM-D score at r ≥ 0.7 (pre-specified performance goal) using Pearson correlation. Key ML-Specific Steps:
- Data Pipeline: Raw sensor data is processed on-device into engineered features (e.g., sleep duration, step count variance, speech rate mean). Only features, not raw audio/ GPS, are transmitted to a secure server.
- Blinded Validation: The locked ML model (algorithmic protocol v1.0) is applied to the feature dataset from weeks 11-12. The statistician generating the composite score is blinded to the HAM-D outcomes.
- Bias Assessment: Pre-specified subgroup analysis (by age, sex, race) to evaluate correlation consistency. A difference in correlation coefficient >0.2 between any major subgroup and the overall population triggers a bias investigation as per PCCP.
- PCCP Trigger: If validation succeeds, the PCCP authorizes the model's use for exploratory endpoint analysis in the sponsor's subsequent Phase III trial. Any model retraining requires a new protocol amendment.
Protocol 2: Implementing a PCCP for Model Adaptation Title: Monitoring and Controlled Update of a Post-Operative Pain Prediction Model Using Federated Learning. Objective: To establish an ethical framework for updating a behavioral ML model with new site data without centralizing sensitive patient information. Design: Multi-center, federated learning implementation. Initial Model: A model trained on historical data to predict severe pain episodes based on pre-operative anxiety scores (ePRO) and early post-operative mobility (wearable). PCCP-Governed Workflow:
- Pre-Specified Performance Thresholds: Model update is triggered if prediction accuracy (AUC) on new site data drops below 0.75 for two consecutive months.
- Pre-Specified Update Method: Federated Averaging (FedAvg) is the locked update algorithm. Each site trains the model locally for 5 epochs on its new data. Only model weight updates (not patient data) are shared to a central server for averaging.
- Pre-Specified Guardrails: Update is only permitted if the new aggregated model maintains AUC > 0.8 on a held-out central validation set representing demographic diversity. A fairness check (equalized odds difference < 0.05) across subgroups is mandated.
- Documentation & Reporting: Each federated update cycle is logged as a "Model Version" in the trial's master file. A summary report is generated for regulatory inspection, detailing performance pre- and post-update, and confirming guardrail adherence.
Visualizations
Title: Integrated ML Protocol Lifecycle from Design to Update
Title: Federated Learning Update Cycle Under a PCCP
The Scientist's Toolkit: Research Reagent Solutions for ML Behavioral Research
| Item/Category | Function in Protocol | Example/Note |
|---|---|---|
| Regulatory-grade DHT Platform | Provides validated sensors (e.g., accelerometer, microphone) and consistent data capture across devices. Essential for reproducible feature engineering. | Apple ResearchKit, BioTel eCOA, proprietary FDA-cleared wearable suites. |
| Feature Engineering Pipeline | Transforms raw, high-frequency sensor data into structured, analyzable features (e.g., RMSSD for heart rate variability). Must be locked and version-controlled. | Custom Python/R scripts using libraries like tsfresh or HeartPy, deployed in a containerized environment. |
| Federated Learning Framework | Enables model training across decentralized data silos without transferring raw data. Key for privacy and multi-site PCCP execution. | NVIDIA FLARE, OpenFL, Flower, or PySyft. |
| Model Monitoring & Bias Detection Toolkit | Tracks model performance drift and fairness metrics (e.g., disparate impact) against pre-set guardrails in real-time. | Arize AI, Fiddler AI, WhyLabs, or custom dashboards using SHAP and Fairlearn. |
| Audit Trail & Versioning System | Logs all model changes, data inputs, and hyperparameters. Critical for demonstrating compliance with the PCCP and E6(R3) data integrity principles. | DVC (Data Version Control), MLflow, Neptune.ai, or integrated electronic trial master file (eTMF). |
| Synthetic Data Generator | Creates artificial behavioral datasets for stress-testing models or augmenting training data in rare populations, mitigating privacy and bias risks. | Mostly AI, Syntegra, or using GANs (Generative Adversarial Networks) like CTGAN. |
The integration of machine learning (ML) into behavioral data collection, particularly within clinical and pharmacological research, necessitates a rigorous re-evaluation of ethical protocols. These protocols, while essential for participant welfare and data integrity, introduce significant trade-offs between speed, financial cost, and scientific rigor. This analysis, framed within a thesis on ML protocols for ethical behavioral data collection, examines these trade-offs through the lens of contemporary research practices. The objective is to provide researchers and drug development professionals with a structured framework to optimize their ethical and methodological approaches without compromising on quality or efficiency.
Quantitative Analysis of Protocol Trade-offs
Recent data from institutional review board (IRB) processing times, cloud computing costs for anonymization, and study replication rates highlight the tangible impacts of ethical oversight. The following tables synthesize current metrics relevant to behavioral studies incorporating ML.
Table 1: Comparative Timeline Impact of Ethical Protocol Stages
| Protocol Stage | Standard Review (Duration) | Expedited Review (Duration) | Key Rigor Factors Affected |
|---|---|---|---|
| IRB/ERC Proposal Preparation | 4-6 weeks | 2-3 weeks | Study design completeness, statistical power analysis |
| Initial Review Cycle | 8-12 weeks | 3-6 weeks | Risk mitigation strategies, inclusion/exclusion criteria |
| Informed Consent Process | 2-3 weeks (in-person) | 1-2 weeks (digital/ eConsent) | Participant comprehension, autonomy, recruitment bias |
| Data Anonymization Setup | 3-4 weeks (manual rules) | 1-2 weeks (automated ML tools) | Data utility, re-identification risk, feature integrity |
| Ongoing Monitoring & Auditing | Continuous (High manual load) | Continuous (ML-assisted, lower load) | Protocol adherence, adverse event detection |
Table 2: Cost-Benefit Analysis of Data Anonymization Techniques
| Anonymization Method | Approximate Cost per 100k Records | Time Required | Re-identification Risk | Data Utility for ML Training |
|---|---|---|---|---|
| Manual Redaction & Pseudonymization | $5,000 - $10,000 | High (Weeks) | Low (if thorough) | High (No algorithmic distortion) |
| Rule-Based Automated Scrubbing | $500 - $2,000 (Cloud compute) | Medium (Days) | Medium (Pattern-based) | Medium-High (Limited distortion) |
| Differential Privacy (Basic) | $1,000 - $3,000 (Compute + expertise) | Low (Hours) | Very Low | Low-Medium (Controlled noise injection) |
| Synthetic Data Generation (ML-based) | $3,000 - $8,000 (Model training) | Medium-High (Initial training) | Extremely Low | Variable (Depends on model fidelity) |
| Federated Learning (No raw data export) | $4,000 - $12,000 (Infrastructure) | Low (After setup) | Minimal | High (Trains on decentralized data) |
Detailed Experimental Protocols
This section provides detailed methodologies for key experiments or processes cited in the trade-off analysis.
Protocol 3.1: Implementing a Federated Learning Workflow for Multi-Site Behavioral Data Collection
Aim: To train an ML model on sensitive behavioral data (e.g., smartphone typing dynamics for early neurodegenerative symptom detection) across multiple institutions without centralizing raw data, thereby enhancing privacy and reducing regulatory burden.
Materials: See "Research Reagent Solutions" (Section 5.0). Procedure:
- Model Initialization: A central coordinator initializes a global machine learning model (e.g., a recurrent neural network) and defines the architecture and hyperparameters.
- Local Training Round: a. The global model is distributed to each participating research site (node). b. Each node trains the model locally on its own ethical-review-approved behavioral dataset for a predetermined number of epochs. c. Training uses site-specific secure computational resources. No raw or labeled data leaves the node.
- Model Aggregation: Each node sends only the updated model parameters (gradients or weights) to the central coordinator using encrypted communication.
- Secure Aggregation: The coordinator aggregates the received parameters using a secure algorithm (e.g., Federated Averaging) to create an improved global model.
- Iteration: Steps 2-4 are repeated for multiple rounds until the global model converges to a satisfactory performance level.
- Validation: A separate, held-out validation dataset (which may be centralized with full ethical approval) is used to evaluate the final global model's performance.
Ethical & Rigor Notes: This protocol significantly reduces the need for complex data transfer agreements and central IRB review for raw data, speeding up multi-site collaboration. Rigor is maintained through standardized local training protocols and secure aggregation methods. The primary cost is in computational infrastructure and expertise.
Protocol 3.2: Comparative Rigor Assessment of eConsent vs. Traditional Consent
Aim: To quantitatively evaluate the impact of an electronic, interactive consent (eConsent) platform on participant comprehension, engagement duration, and recruitment rate compared to traditional paper-based consent.
Materials: eConsent software platform (e.g., REDCap, specialized eConsent tool), validated comprehension questionnaire, timing software, participant recruitment pool. Procedure:
- Design: Randomized controlled trial. Participants eligible for a simulated behavioral monitoring study are randomly assigned to Group A (eConsent) or Group B (Traditional Paper Consent).
- Intervention: a. Group A: Completes the consent process via an interactive eConsent module containing embedded videos, glossaries, and comprehension checkpoints. b. Group B: Completes the consent process using a standard PDF/paper document with a researcher available for questions.
- Data Collection: a. Record total time spent in the consent process for each participant. b. Administer a standardized, 10-item multiple-choice comprehension test immediately after consent is given. c. Record the recruitment yield (percentage who consent to proceed) for each group.
- Analysis: a. Compare mean comprehension scores between groups using a t-test. b. Compare median consent times using a non-parametric test. c. Compare recruitment yields using a chi-square test.
Ethical & Rigor Notes: This meta-experiment itself requires IRB approval. It directly measures the trade-off: eConsent may reduce time and cost per participant and potentially improve comprehension (rigor), but may exclude populations with low digital literacy, introducing bias.
Mandatory Visualizations
Diagram Title: Federated Learning Workflow for Ethical Data Collection
Diagram Title: Core Tensions in Ethical Protocol Design
The Scientist's Toolkit: Research Reagent Solutions
Table 3: Essential Materials for Ethical ML Behavioral Research
| Item/Reagent/Solution | Primary Function in Ethical Protocols |
|---|---|
| eConsent Platform (e.g., REDCap, DocuSign) | Facilitates interactive, documented informed consent process; improves comprehension tracking and reduces administrative time. |
| Federated Learning Software Stack (e.g., PySyft, TensorFlow Federated) | Enables model training across decentralized data silos, minimizing privacy risks and data transfer compliance overhead. |
| Differential Privacy Library (e.g., Google DP, OpenDP) | Provides algorithms to add mathematical noise to datasets or queries, ensuring individual records cannot be re-identified in analyses. |
| Synthetic Data Generation Tool (e.g., Synthea, Gretel.ai) | Creates statistically similar but artificial datasets for method development and piloting, reducing initial need for real sensitive data. |
| Secure Multi-Party Computation (MPC) Framework | Allows joint analysis on data from multiple parties where no single party sees the others' raw data, crucial for secure collaborations. |
| Automated Anonymization Pipeline (e.g., Presidio, Amazon Comprehend) | Uses NLP to automatically detect and redact Personally Identifiable Information (PII) from unstructured text (e.g., interview transcripts). |
| Blockchain-based Audit Trail System | Provides an immutable, timestamped ledger of data access and model changes, ensuring transparency and accountability for regulatory audits. |
| Behavioral Research Platform (e.g., Empatica E4, Beiwe) | Provides a validated, ethical framework for collecting passive sensor data (GPS, accelerometer) from participants' devices with built-in consent management. |
Conclusion
The development of ethical ML protocols for behavioral data is not a barrier to innovation but a foundational requirement for credible and sustainable research. By embedding core ethical principles from study design through deployment and validation, researchers can harness the richness of behavioral data while upholding participant rights and regulatory compliance. The integration of privacy-preserving technologies like federated learning and differential privacy demonstrates that methodological rigor and ethical safeguards can coexist. Moving forward, the field must prioritize standardized ethical benchmarking, cross-industry collaboration on guidelines, and the development of audit-ready ML systems. For drug development, these protocols promise more ecologically valid endpoints, accelerated digital biomarker discovery, and ultimately, therapies developed with a deeper, more respectful understanding of patient behavior and experience. The future of clinical research depends on building this trust through technology.